實驗
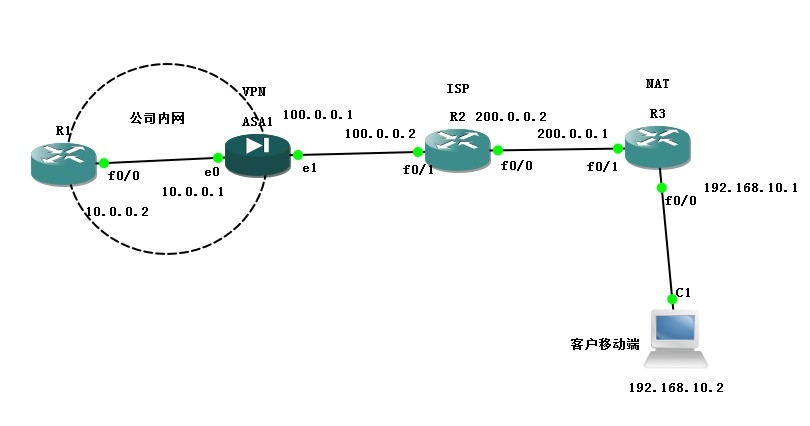
實驗拓撲圖:
實驗步驟:
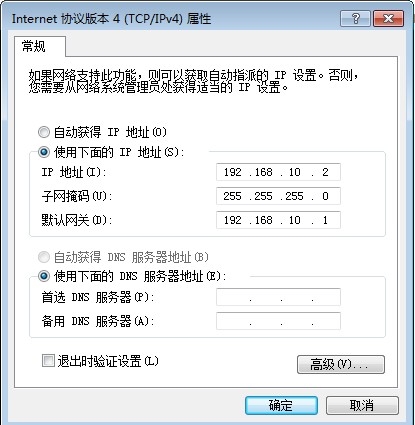
路由器和PC機地址規劃:
R1(config)#int f0/0
R1(config-if)#ip add 10.0.0.2 255.255.255.0
R1(config-if)#no shut
R2(config)#int f0/1
R2(config-if)#ip add 100.0.0.2 255.255.255.252
R2(config-if)#no shut
R2(config-if)#int f0/0
R2(config-if)#ip add 200.0.0.2 255.255.255.252
R2(config-if)#no shut
R3(config)#int f0/1
R3(config-if)#ip add 200.0.0.1 255.255.255.252
R3(config-if)#no shut
R3(config-if)#int f0/0
R3(config-if)#ip add 192.168.10.1 255.255.255.0
R3(config-if)#no shut
ciscoasa(config)# int e0/0
ciscoasa(config-if)# ip add 10.0.0.1 255.255.255.0
ciscoasa(config-if)# no shut
ciscoasa(config-if)# nameif inside
ciscoasa(config-if)# int e0/1
ciscoasa(config-if)# ip add 100.0.0.1 255.255.255.252
ciscoasa(config-if)# no shut
ciscoasa(config-if)# nameif outside
配置NAT:
R3(config)#access-list 1 permit 192.168.10.0 0.0.0.255
R3(config)#ip nat inside source list 1 in f0/1 overload
R3(config)#int f0/1
R3(config-if)#ip nat out
R3(config-if)#int f0/0
R3(config-if)#ip nat in
配置默認路由:
R1(config)#ip route 0.0.0.0 0.0.0.0 10.0.0.1
R3(config)#ip route 0.0.0.0 0.0.0.0 200.0.0.2
ciscoasa(config)# route outside 0 0 100.0.0.2
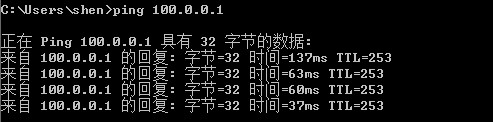
測試PC機是否ping通對端***設備:
在ASA上配置Easy***:
ciscoasa(config)# crypto isakmp enable outside //開啓isakmp
ciscoasa(config)# access-list 110 extended permit ip 10.0.0.0 255.255.255.0 any //定義客戶端感興趣流量
ciscoasa(config)# ip local pool vip 10.0.0.50-10.0.0.60 mask 255.255.255.0 //定義客戶端的IP地址範圍
ciscoasa(config)# username zhangsan password 123123 //設置防火牆登陸的賬戶和密碼
ciscoasa(config)# crypto isakmp policy 1
ciscoasa(config-isakmp-policy)# authentication pre-share
ciscoasa(config-isakmp-policy)# encryption 3des
ciscoasa(config-isakmp-policy)# hash sh
ciscoasa(config-isakmp-policy)# group 2
ciscoasa(config)# group-policy gpolicy internal //建立內置組策略
ciscoasa(config)# group-policy gpolicy attributes //配置策略屬性
ciscoasa(config-group-policy)# split-tunnel-policy tunnelspecified //定義所有指定的流量可以通過隧道
ciscoasa(config-group-policy)# split-tunnel-network-list value 110 ///調用ACL
ciscoasa(config-group-policy)# address-pools value vip //調用地址池
ciscoasa(config)# tunnel-group ez*** type ipsec-ra //定義隧道組並指定類型爲遠程訪問
ciscoasa(config)# tunnel-group ez*** general-attributes //指定屬性
ciscoasa(config-tunnel-general)# default-group-policy gpolicy //調用組策略
ciscoasa(config-tunnel-general)# ex
ciscoasa(config)# tunnel-group ez*** ipsec-attributes //設置預共享密鑰
ciscoasa(config-tunnel-ipsec)# pre-shared-key abc123
ciscoasa(config-tunnel-ipsec)# ex
ciscoasa(config)# crypto ipsec transform-set bset esp-3des esp-sha-hmac ///定義傳輸集
ciscoasa(config)# crypto dynamic-map dmap 1 set transform-set bset //動態map中調用傳輸集
ciscoasa(config)# crypto map bmap 1 ipsec-isakmp dynamic dmap //靜態map調用動態map
ciscoasa(config)# crypto map bmap in outside //靜態map調用在端口
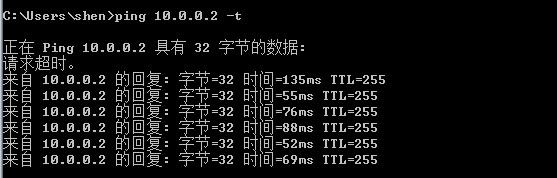
測試客戶端訪問與內網通信:
實驗完成