一、概述
grains是minion啓動時加載,在minion運行過程中不會發生變化,所以是靜態數據。grains數據的定製可以在各minion端,也可以放在master端;grains中包含許多的信息,如:運行的內核版本,操作系統,網絡接口地址,MAC地址,cpu,內存等等信息。
Pillar主要用來保存各minion自定義變量;是Salt用來分發變量到所有或指定minion的一個定製接口,所以相對grains來說可以稱爲動態的數據,保存在master端。
本文將基於pillar爲各主機定製要開放的白名單ip和要開放的對外服務,以及自身要出去訪問的服務;因爲線上防火牆默認規則是drop的,因此需要定義以上三種規則,以上三種規則將在pillar和salt配置中體現。
本文測試環境可以是redhat系統 CentOS6 或7,基於iptables saltstack版本2016.10上測試 通過;我想邏輯應該是一樣的;
saltstack redhat繫上yum源地址
salt安裝配置這裏忽略可查看之前文章
二、配置主機pillar
1、針對10.8.11.171配置防火牆規則,pillar定義規則
# cat /srv/pillar/top.sls
base:
10.8.11.171:
- webname.web10-8-11-125
- hosts.hosts10_8_11_125
- iptables.open.web
- iptables.access.ntp
- iptables.access.web
- iptables.access.sms
- iptables.whiteip.offices
# cat /srv/pillar/iptables/whiteip/offices.sls
white_ips:
allow_offices1:
allowip: 10.8.0.0/16
allow_offices2:
allowip: 61.188.188.188
###對外開放web服務配置,其他配置類似
# cat /srv/pillar/iptables/open/web.sls
open_allow:
http_open_allow:
port: 80
procto: 'tcp'
### 訪問外面的服務,其他訪問服務類似
#cat /srv/pillar/iptables/access/ntp.sls
out_allow:
ntp_out_allow:
port: 123
procto: 'udp'
說明:下次10.8.11.171主機要開放服務時就修改/srv/pillar/top.sls文件掛載要開放的服務(- iptables.open.xxx)這個xxx要在/srv/pillar/iptables/open/目錄下xxx.sls 格式如前頁的web.sls;添加出去訪問服務時(- iptables.access.yyy)這個yyy要在/srv/pillar/iptables/access/yyy.sls格式如前面的ntp.sls;當要添加白名單ip服務時(- iptables.whiteip.zzz)這個zzz.sls 要在/srv/pillar/iptables/whiteip/zzz.sls 格式類似offices.sls
2、salt state配置
cat /srv/salt/top.sls
base:
10.8.11.171:
- base.env_init
- iptables.init
- nginx.env_init
- php.env_init
# cat /srv/salt/iptables/init.sls
###### 清空原規則 ######
clear_iptables:
cmd.run:
{% if grains['osfinger'] == 'CentOS-6' %}
- name: echo >/etc/sysconfig/iptables && service iptables stop
{% elif grains['osfinger'] == 'CentOS Linux-7' %}
- name: echo >/etc/sysconfig/iptables && systemctl stop iptables
{% endif %}
#### 添加白名單ip
{% for fw, rule in pillar['white_ips'].iteritems() %}
{{ fw }}_INPUT:
iptables.insert:
- position: 1
- table: filter
- chain: INPUT
- jump: ACCEPT
- match: state
- connstate: NEW,ESTABLISHED
- source: {{ rule['allowip'] }}
- comment: {{ rule['comm'] }}
- save: True
{{ fw }}_OUTPUT:
iptables.insert:
- position: 1
- table: filter
- chain: OUTPUT
- jump: ACCEPT
- match: state
- connstate: NEW,ESTABLISHED
- destination: {{ rule['allowip'] }}
- save: True
{% endfor %}
# 允許ping入
allow_icmp_INPUT:
iptables.append:
- table: filter
- chain: INPUT
- jump: ACCEPT
- match: state
- connstate: NEW,ESTABLISHED
- protocol: icmp
- comment: "Allow Ping IN"
- save: True
# 允許ping出
allow_ping_OUTPUT:
iptables.append:
- table: filter
- chain: OUTPUT
- jump: ACCEPT
- match: state
- connstate: NEW,RELATED,ESTABLISHED
- protocol: icmp
- comment: "Allow Ping OUT"
- save: True
# 允許訪問外網服務
{% for fw, rule in pillar['out_allow'].iteritems() %}
{{ fw }}_INPUT:
iptables.insert:
- position: 2
- table: filter
- chain: INPUT
- jump: ACCEPT
- match: state
- connstate: ESTABLISHED
- protocol: {{ rule['procto'] }}
- sport: {{ rule['port'] }}
- save: True
{{ fw }}_OUTPUT:
iptables.insert:
- position: 2
- table: filter
- chain: OUTPUT
- jump: ACCEPT
- match: state
- connstate: NEW,RELATED,ESTABLISHED
- protocol: {{ rule['procto'] }}
- dport: {{ rule['port'] }}
- save: True
{% endfor %}
###### 獲取自定義需要開放的服務端口並加入iptables規則中(同時取消狀態追蹤) ######
{% for eachfw, fw_rule in pillar['open_allow'].iteritems() %}
{{ eachfw }}_INPUT:
iptables.insert:
- position: 1
- table: filter
- chain: INPUT
- jump: ACCEPT
- match: state
- connstate: NEW,ESTABLISHED
- protocol: {{ fw_rule['procto'] }}
- dport: {{ fw_rule['port'] }}
- save: True
{{ eachfw }}_OUTPUT:
iptables.insert:
- position: 1
- table: filter
- chain: OUTPUT
- jump: ACCEPT
- match: state
- connstate: ESTABLISHED
- sport: {{ fw_rule['port'] }}
- protocol: {{ fw_rule['procto'] }}
- save: True
{{ eachfw }}_NOTRACK_FROM_OUTPUT:
iptables.insert:
- position: 1
- table: raw
- chain: OUTPUT
- jump: NOTRACK
- match: state
- connstate: ESTABLISHED
- sport: {{ fw_rule['port'] }}
- protocol: {{ fw_rule['procto'] }}
- save: True
{{ eachfw }}_NOTRACK_TO_OUTPUT:
iptables.insert:
- position: 1
- table: raw
- chain: OUTPUT
- jump: NOTRACK
- match: state
- connstate: ESTABLISHED
- dport: {{ fw_rule['port'] }}
- protocol: {{ fw_rule['procto'] }}
- save: True
{{ eachfw }}_NOTRACK_FROM_PREROUTING:
iptables.insert:
- position: 1
- table: raw
- chain: PREROUTING
- jump: NOTRACK
- match: state
- connstate: ESTABLISHED
- sport: {{ fw_rule['port'] }}
- protocol: {{ fw_rule['procto'] }}
- save: True
{{ eachfw }}_NOTRACK_TO_PREROUTING:
iptables.insert:
- position: 1
- table: raw
- chain: PREROUTING
- jump: NOTRACK
- match: state
- connstate: ESTABLISHED
- dport: {{ fw_rule['port'] }}
- protocol: {{ fw_rule['procto'] }}
- save: True
{% endfor %}
# 設置INPUT默認策略爲DROP
default_to_INPUT:
iptables.set_policy:
- chain: INPUT
- policy: DROP
- save: True
# 設置OUTPUT默認策略爲DROP
default_to_OUTPUT:
iptables.set_policy:
- chain: OUTPUT
- policy: DROP
- save: True
# 設置FORWARD默認策略爲DROP
default_to_FORWARD:
iptables.set_policy:
- chain: FORWARD
- policy: DROP
- save: True
###### 重啓iptables 並保持開機自動加載 ######
iptables-service:
service.running:
- name: iptables
- reload: True
- enable: True
說明:在推送iptables規則前清除已有的規則;再從pillar的配置文件循環讀取並配置防火規則;最後設置iptables默認策略INPUT OUTPUT FORWARD 爲DROP; 有人可能就要問了,爲舍搞這麼複雜,防火開起來開放一些規則就行了,爲啥非得把默認策略設置DROP,進出都得要規則?如果這麼問請看下這裏~
三、規則推送
1、查看主機的pillar
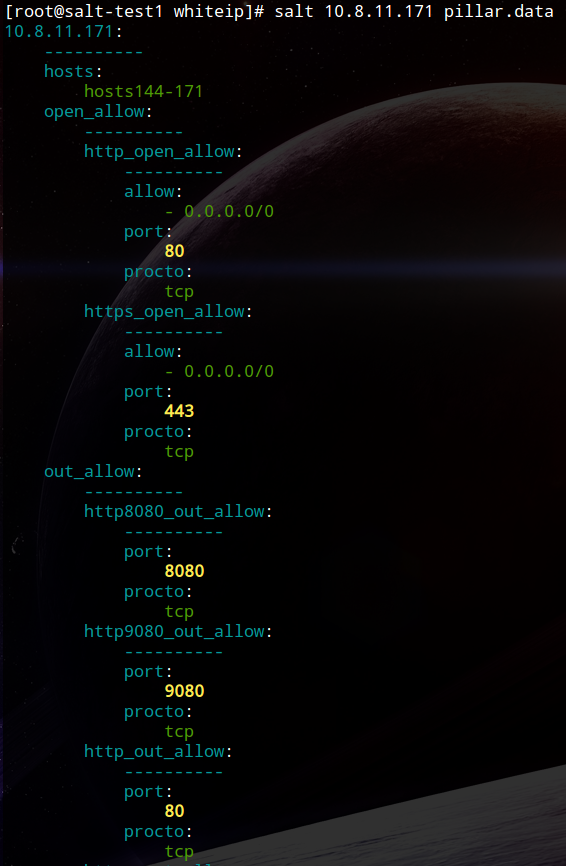
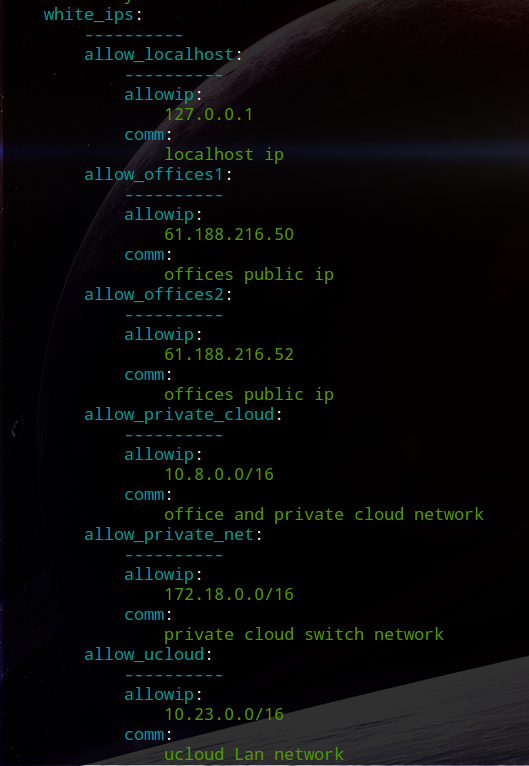
# salt 10.8.11.171 pillar.data如圖:可以看出以上的配置白名單ip與開放和訪問服務端口
2、推送到主機
# salt 10.8.11.171 state.sls iptables.init
最後出現類似下面的表示已經推送配置成功
Summary for 10.8.11.171
-------------
Succeeded: 43 (changed=42)
Failed: 0
-------------
Total states run: 43
Total run time: 3.120 s
### 查看iptables 配置
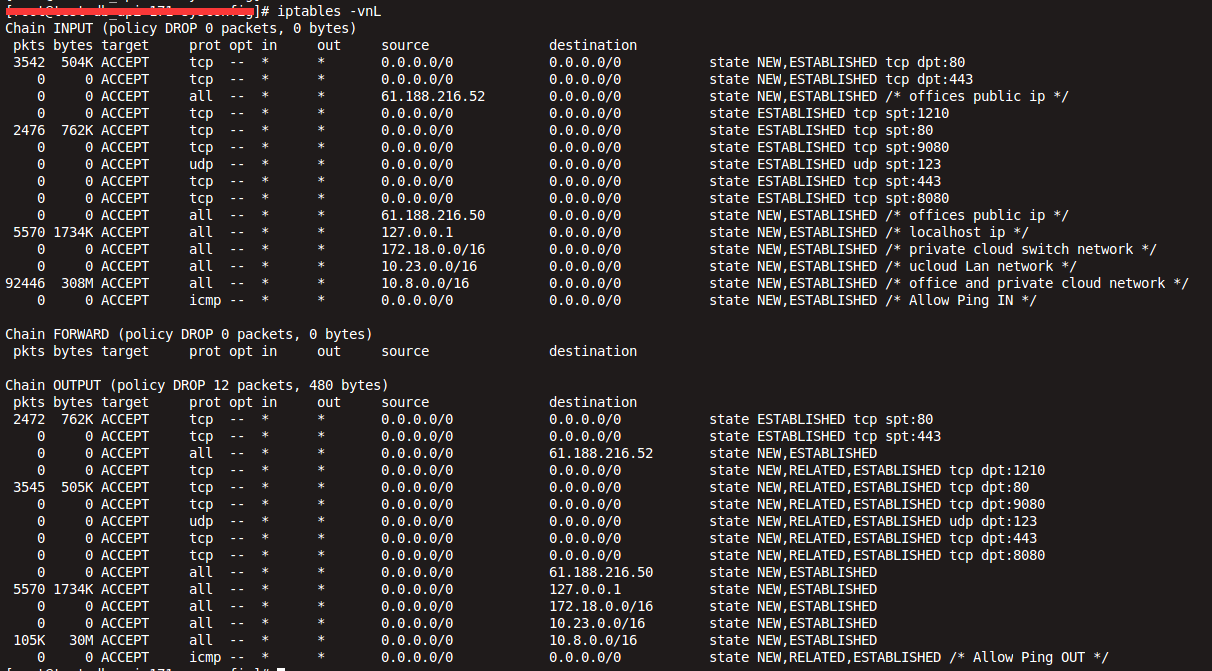
# iptables -vnL如圖:
開放的白名單和開放的服務以及能出去訪問的服務已經都有了;另外默認策略已經是DROP;這樣只有開放的白名單和允許出去訪問服務才能出去,很好的阻止了反彈式木-馬主動出去訪問的情況,同時只允許開放的服務才能進來;其他情況一律拒絕;不過需要注意的是,在生產線上改造時,勿必確認好主機開放的服務和需要出去訪問或調用其他主機的服務端口,否則會誤傷,你懂滴!爲什麼非得搞這麼嚴格這麼麻煩,這樣安全啊,防止反彈式木-馬效果好呀~!
至些salt 通過pillar 配置防火牆規則完成!
本文基於生產線salt配置,是整理備忘,如有不妥之處歡迎指正與交流 !謝謝~