Ipsec簡介
IPSec(InternetProtocolSecurity)是安全聯網的長期方向。它通過端對端的安全性來提供主動的保護以防止專用網絡與 Internet 的***。在通信中,只有發送方和接收方纔是唯一必須瞭解 IPSec 保護的計算機。在 Windows 2000、Windows XP 和 Windows Server 2003 家族中,IPSec 提供了一種能力,以保護工作組、局域網計算機、域客戶端和服務器、分支機構(物理上爲遠程機構)、Extranet 以及漫遊客戶端之間的通信。
IPsec與其它互聯網安全協議的對比
2作用目標編輯
保護 IP 數據包的內容。
通過數據包篩選及受信任通訊的實施來防禦網絡***。
這兩個目標都是通過使用基於加密的保護服務、安全協議與動態密鑰管理來實現的。這個基礎爲專用網絡計算機、域、站點、遠程站點、Extranet 和撥號用戶之間的通信提供了既有力又靈活的保護。它甚至可以用來阻礙特定通訊類型的接收和發送。
其中以接收和發送最爲重要。
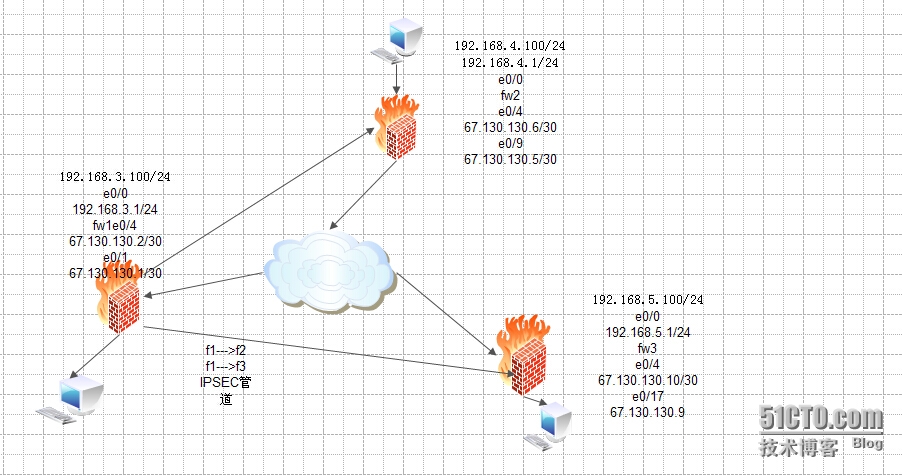
拓撲圖
配置三層交換機
<Quidway>sys
[Quidway]sys isp
[isp]vlan 10
[isp-vlan10]port e0/1
[isp-vlan10]vlan 20
[isp-vlan20]port e0/9
[isp-vlan20]vlan 30
[isp-vlan30]port e0/17
[isp-vlan30]int vlan10
[isp-Vlan-interface10]ip add 67.130.130.1 255.255.255.252
[isp-Vlan-interface10]int vlan 20
[isp-Vlan-interface20]ip add 67.130.130.5 255.255.255.252
[isp-Vlan-interface20]int vlan 30
[isp-Vlan-interface30]ip add 67.130.130.9 255.255.255.252
設置fw1
<H3C>sys
[H3C]sys fw1
[fw1]int eth0/0
[fw1-Ethernet0/0]ip add 192.168.3.1 24
[fw1-Ethernet0/0]loopback
[fw1-Ethernet0/0]int eth0/4
[fw1-Ethernet0/4]ip add 67.130.130.2 30
取消端口隔離
[fw1]undo insulate
添加eth0/4到untrust
[fw1]firewall zone untrust
[fw1-zone-untrust]add int eth0/4
添加eth0/0到trust
[fw1]firewall zone trust
[fw1-zone-trust]add int eth0/0
用訪問控制列表篩選
[fw1]acl number 3000 match-order auto
[fw1-acl-adv-3000]rule 10 permit ip source 192.168.3.0 0.0.0.255destination 192.168.4.0 0.0.0.255
[fw1-acl-adv-3000]rule 20 deny ip source any destination any
創建安全提議tran1
[fw1]ipsec proposal tran1
選擇管道方式
[fw1-ipsec-proposal-tran1]encapsulation-mode tunnel
選擇安全協議sep
[fw1-ipsec-proposal-tran1]transform esp
完整性校驗選md5
[fw1-ipsec-proposal-tran1]esp authentication-algorithm md5
加密算法選des
[fw1-ipsec-proposal-tran1]esp encryption-algorithm des
設置ike peer
[fw1]ike peer fw2
設置來源ip
[fw1-ike-peer-fw2]local-address 67.130.130.2
設置目標ip
[fw1-ike-peer-fw2]remote-address 67.130.130.6
設置密鑰
[fw1-ike-peer-fw2]pre-shared-key 123456
注意,這個密鑰一定要記住,下面還要用到
isa和篩選流相結合
選擇動態isa
[fw1]ipsec policy policy1 10 isakmp
篩選符合3000表的流
[fw1-ipsec-policy-isakmp-policy1-10]security acl 3000
選擇符合提議tran1的
[fw1-ipsec-policy-isakmp-policy1-10]proposal tran1
選擇ike 對等體爲fw2
[fw1-ipsec-policy-isakmp-policy1-10]ike-peer fw2
進入端口eth0/4應用策略
[fw1]int eth0/4
[fw1-Ethernet0/4]ipsec policy policy1
第一條隧道已經設置好了,接着該去設置這條隧道的另一端,進入防火牆fw2
下面是第二條隧道的設置
[fw1]acl number 3001 match-order auto
[fw1-acl-adv-3001]rule permit ip source 192.168.3.0 0.0.0.255destination 192.168.5.0 0.0.0.255
[fw1-acl-adv-3001]rule deny ip source any destination any
[fw1]ipsec proposal tran2
[fw1-ipsec-proposal-tran2]encapsulation-mode tunnel
[fw1-ipsec-proposal-tran2]transform esp
[fw1-ipsec-proposal-tran2]esp authentication-algorithm md5
[fw1-ipsec-proposal-tran2]esp encryption-algorithm des
[fw1]ike peer fw3
[fw1-ike-peer-fw3]local-address 67.130.130.2
[fw1-ike-peer-fw3]remote-address 67.130.130.10
[fw1-ike-peer-fw3]pre-shared-key 654321
[fw1]acl number 3001 match-order auto
[fw1-acl-adv-3000]undo rule 20
設置fw2
<H3C>sys
[H3C]sys fw2
[fw2]int eth0/0
[fw2-Ethernet0/0]ip add 192.168.4.1 24
[fw2-Ethernet0/0]loopback
[fw2-Ethernet0/0]int eth0/4
[fw2-Ethernet0/4]ip add 67.130.130.6 30
[fw2]undo insulate
[fw2]firewall packet-filter default permit
[fw2]firewall zone trust
[fw2-zone-trust]add interface eth0/0
[fw2]firewall zone untrust
[fw2-zone-untrust]add int eth0/4
[fw2]ip route-static 0.0.0.0 0 67.130.130.5
[fw2]acl number 3000 match-order auto
[fw2-acl-adv-3000]rule 10 permit ip source 192.168.4.0 0.0.0.255destination 192.168.3.0 0.0.0.255
[fw2-acl-adv-3000]rule 20 deny ip source any destination any
[fw2]ipsec proposal tran1
[fw2-ipsec-proposal-tran1]encapsulation-mode tunnel
[fw2-ipsec-proposal-tran1]esp authentication-algorithm md5
[fw2-ipsec-proposal-tran1]esp encryption-algorithm des
[fw2]ike peer fw1
[fw2-ike-peer-fw1]local-address 67.130.130.6
[fw2-ike-peer-fw1]remote-address 67.130.130.2
[fw2-ike-peer-fw1]pre-shared-key 123456
這個密鑰要和另外一端的一樣
[fw2]ipsec policy policy1 10 isakmp
[fw2-ipsec-policy-isakmp-policy1-10]security acl 3000
[fw2-ipsec-policy-isakmp-policy1-10]proposal tran1
[fw2-ipsec-policy-isakmp-policy1-10]ike-peer fw1
[fw2]int eth0/4
[fw2-Ethernet0/4]ipsec policy policy1
配置fw3
<H3C>sys
[H3C]sys fw3
[fw3]int eth0/0
[fw3-Ethernet0/0]ip add 192.168.5.1 24
[fw3-Ethernet0/0]loopback
[fw3-Ethernet0/0]int eth0/4
[fw3-Ethernet0/4]ip add 67.130.130.10 30
[fw3]undo insulate
[fw3]firewall zone untrust
[fw3-zone-untrust]add int eth0/4
[fw3]firewall zone trust
[fw3-zone-trust]add int eth0/0
[fw3]ip route-static 0.0.0.0 0 67.130.130.9
[fw3]acl number 3001 match-order auto
[fw3-acl-adv-3001]rule 10 permit ip source 192.168.5.0 0.0.0.255destination 192.168.3.0 0.0.0.255
[fw3-acl-adv-3001]rule 20 deny ip source any destination any
[fw3]ipsec proposal tran2
[fw3-ipsec-proposal-tran2]encapsulation-mode tunnel
[fw3-ipsec-proposal-tran2]transform esp
[fw3-ipsec-proposal-tran2]esp authentication-algorithm md5
[fw3-ipsec-proposal-tran2]esp encryption-algorithm des
[fw3]ike peer fw1
[fw3-ike-peer-fw1]local-address 67.130.130.10
[fw3-ike-peer-fw1]remote-address 67.130.130.2
[fw3-ike-peer-fw1]pre-shared-key 654321
[fw3]ipsec policy policy1 10 isakmp
[fw3-ipsec-policy-isakmp-policy1-10]security acl 3001
[fw3-ipsec-policy-isakmp-policy1-10]tracert tran2
[fw3-ipsec-policy-isakmp-policy1-10]ike-peer fw1
[fw3]int eth0/4
[fw3-Ethernet0/4]ipsec policy policy1