華爲IPSEC-×××-典型配置舉例1-採用手工方式建立IPsec 安全隧道
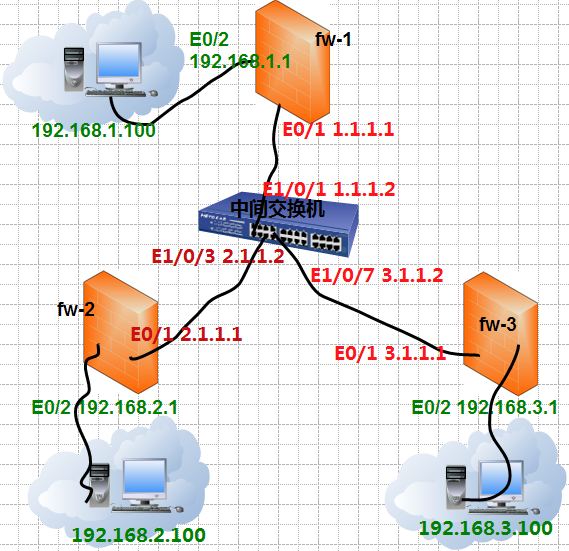
1, 某公司(總部在北京)有兩個子公司分別在上海和廣州,要求通過×××實現公司之間相互通信!
2, 實驗環境如下:要求192.168.1.0/24網段的員工分別與192.168.2.0/24,192.168.3.0/24的員工通信!(中間的爲公網)
3, 本實驗要求採用手工方式建立IPsec 安全隧道
firewall zone trust
add interface Ethernet 0/2
firewall zone untrust
add interface Ethernet 0/1
interface Ethernet0/2
ip address 192.168.1.1 255.255.255.0
interface Ethernet0/1
ip address 1.1.1.1 255.255.255.0
ip route-static 0.0.0.0 0.0.0.0 1.1.1.2 preference 60
firewall zone trust
add interface Ethernet 0/2
firewall zone untrust
add interface Ethernet 0/1
ip address 192.168.2.1 255.255.255.0
interface Ethernet0/1
ip address 2.1.1.1 255.255.255.0
ip route-static 0.0.0.0 0.0.0.0 2.1.1.2 preference 60
firewall zone trust
add interface Ethernet 0/2
firewall zone untrust
add interface Ethernet 0/1
interface Ethernet0/2
ip address 192.168.3.1 255.255.255.0
interface Ethernet0/1
ip address 3.1.1.1 255.255.255.0
ip route-static 0.0.0.0 0.0.0.0 3.1.1.2 preference 60
interface Vlan-interface3
interface Vlan-interface7
interface Vlan-interface10
interface Ethernet0/1
interface Ethernet0/3
interface Ethernet0/7
rule 10 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
rule 20 deny ip source any destination any
rule 10 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
rule 20 deny ip source any destination any
ipsec proposal zhu-1
encapsulation-mode tunnel
esp authentication-algorithm md5
esp encryption-algorithm des
display ipsec proposal
ipsec proposal zhu-2
encapsulation-mode tunnel
esp authentication-algorithm md5
esp encryption-algorithm des
display ipsec proposal
ipsec policy policy1 10 manual
tunnel local 1.1.1.1
tunnel remote 2.1.1.1
sa spi outbound esp 12345
sa spi inbound esp 54321
sa string-key outbound esp zzu
sa string-key inbound esp zzdx
ipsec policy policy1 20 manual
tunnel local 1.1.1.1
tunnel remote 3.1.1.1
sa spi outbound esp 123456
sa spi inbound esp 654321
sa string-key outbound esp abcbef
sa string-key inbound esp qazwsx
interface Ethernet0/1
ipsec policy policy1
display ipsec proposal
rule 10 permit ip source 192.168.2.0 0.0.0.255 dest 192.168.1.0 0.0.0.255
rule 20 deny ip source any dest any
ipsec policy policy2 10 manual
sa spi inbo esp 12345
sa spi outbo esp 54321
sa string inbo esp zzu
sa str outbo esp zzdx
display ipsec proposal
rule 10 permit ip source 192.168.3.0 0.0.0.255 dest 192.168.1.0 0.0.0.255
rule 20 deny ip source any dest any
ipsec policy policy3 20 manual
sa spi inbo esp 123456
sa spi outbo esp 654321
sa string inbo esp abcbef
sa str outbo esp qazwsx
ipsec poli policy3
display ipsec proposal
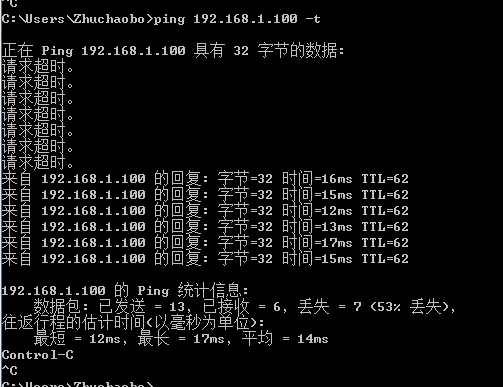
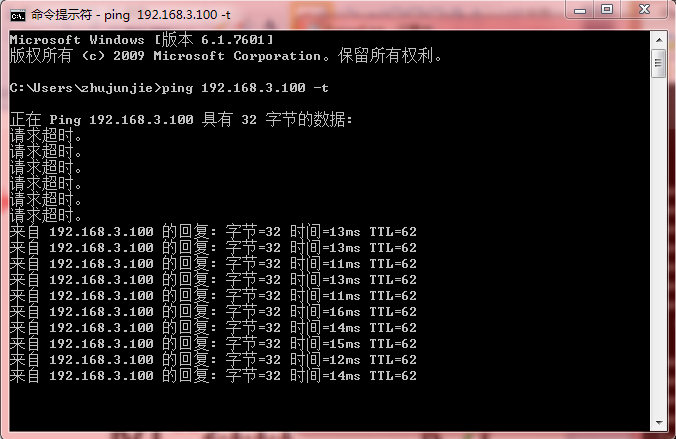
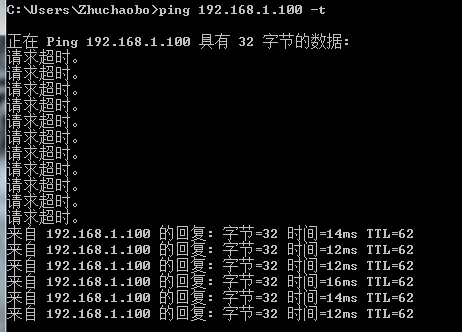
192.168.1.100客戶端ping測試192.168.3.100,應用以後ipsec以後可以通信。
192.168.3.100客戶端ping測試192.168.1.100,應用以後ipsec以後可以通信。
查看fw-1,fw-2.fw-3的ipsec信息和當前配置: