防盜鏈演示
1、安裝配置DNS域名解析服務
[root@localhost ~]# yum install bind -y
[root@localhost ~]# vim /etc/named.conf
options {
listen-on port 53 { any; };
...
allow-query { any; };
[root@localhost ~]# vim /etc/named.rfc1912.zones
zone "accp.com" IN { type master;
file "accp.com.zone";
allow-update { none; };
};
[root@localhost ~]# cd /var/named/
[root@localhost named]# cp -p named.localhost accp.com.zone
#複製模板文件
[root@localhost named]# vim accp.com.zone
$TTL 1D
@ IN SOA @ rname.invalid. (
0 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
NS @
A 127.0.0.1
www IN A 192.168.235.158
#IP地址指向本機地址
[root@localhost named]# systemctl start named
[root@localhost named]# systemctl stop firewalld.service
[root@localhost named]# setenforce 02、打開一臺Win7虛擬機,搭建盜鏈網站。創建一個網頁內容,修改後綴爲index.html
<html>
<head>
<title>雲計算</title>
</head>
<body>
<h1>this is test web</h1>
<img src="http://www.accp.com/game.jpg"/>
</body>
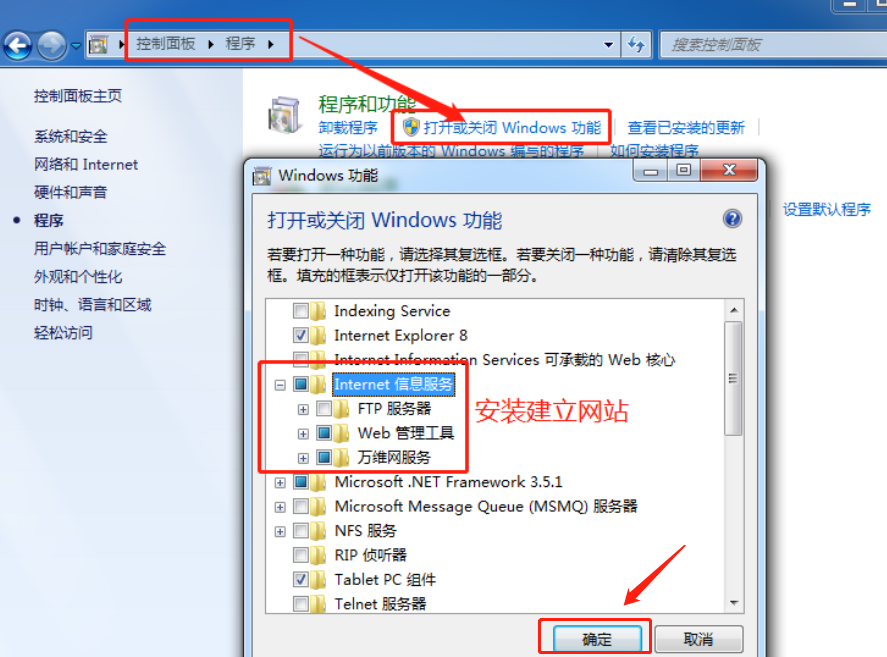
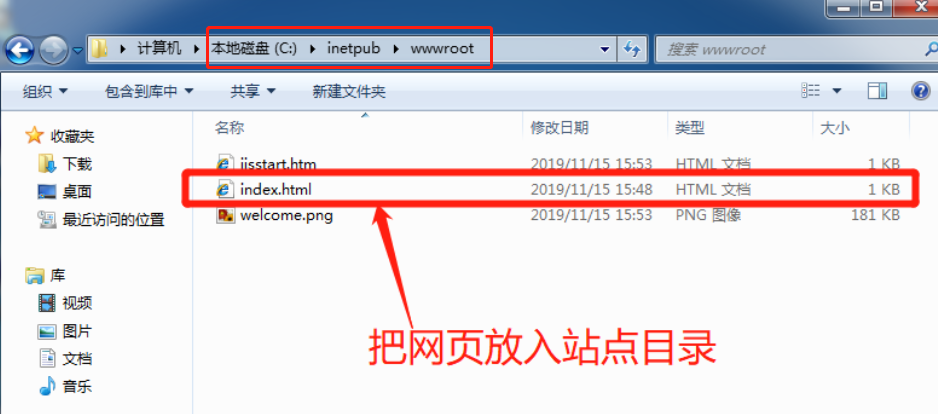
</html>3、搭建網站
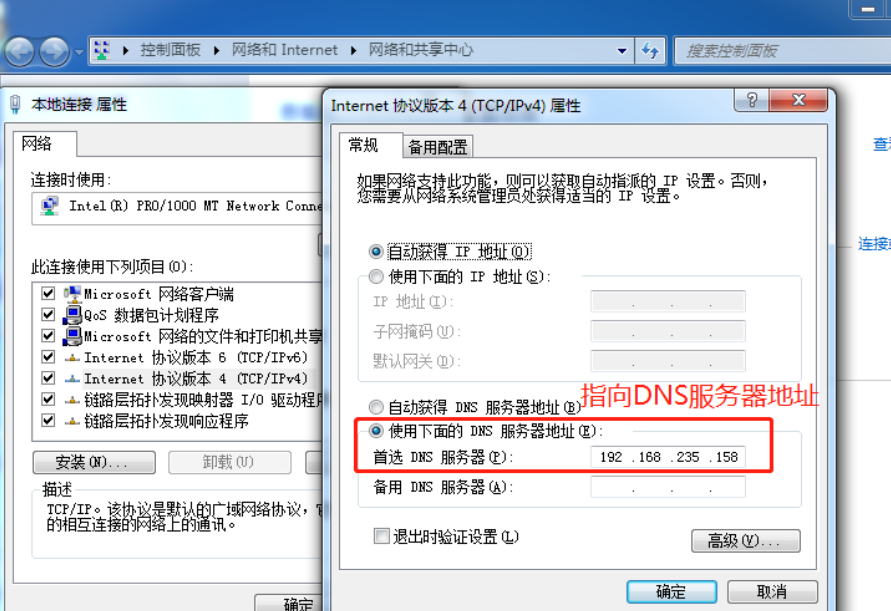
4、修改首選DNS服務器地址
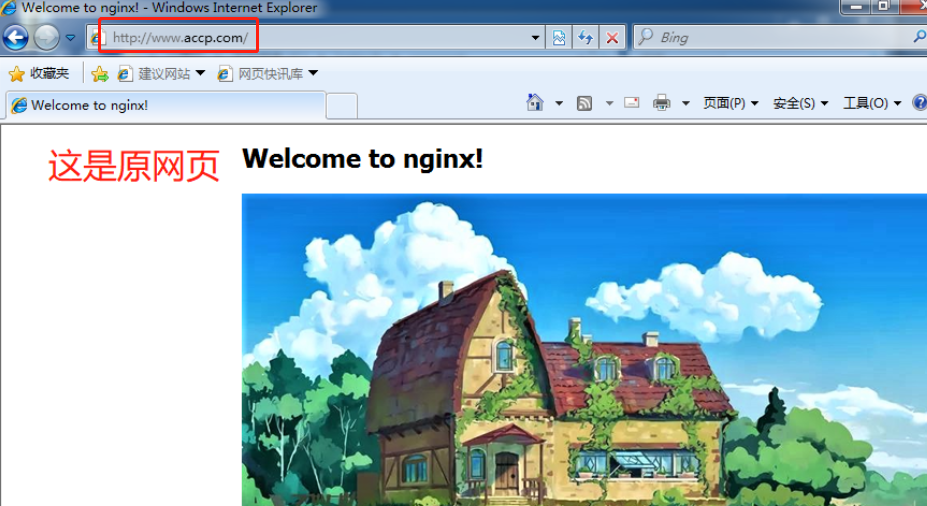
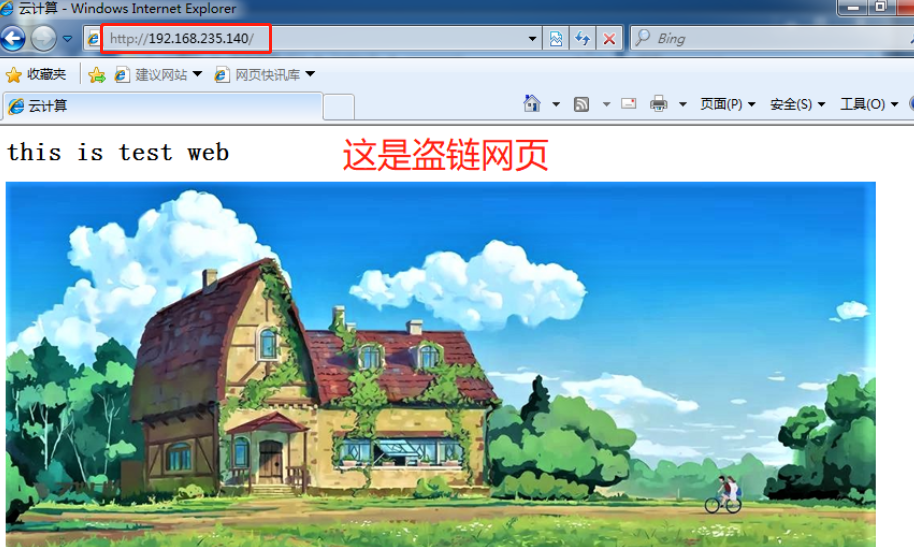
5、分別訪問原網站和盜鏈網站
6、修改Nginx.conf文件
[root@localhost named]# vim /usr/local/nginx/conf/nginx.conf
location ~*\.(jpg|gif|swf)$ {
#支持格式
valid_referers none blocked *.accp.com accp.com;
#允許用accp.com爲後綴訪問
if ( $invalid_referer ) {
#判斷是否被盜鏈
rewrite ^/ http://www.accp.com/error.png;
#判定被盜鏈就跳轉錯誤圖片
}
}
[root@localhost named]# cp /abc/error.png /usr/local/nginx/html/
[root@localhost named]# systemctl stop nginx
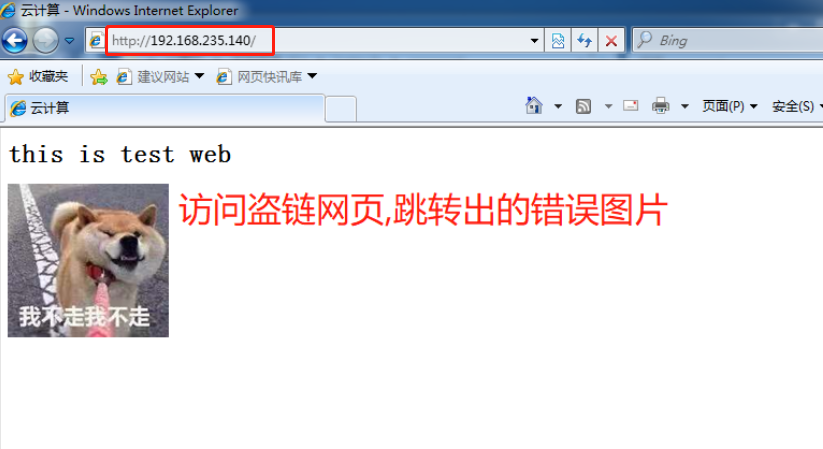
[root@localhost named]# systemctl start nginx7、再次訪問盜鏈網頁,驗證防盜效果