背景
前面介紹了kubernetes集羣部署,如果想更直觀地管理和監控k8s集羣狀況,kubernets-dashboard是一個比較大衆的方式。dashboard提供了一個UI界面,使我們可以在頁面上查看kubernetes的集羣狀態以及對集羣進行相關的操作,大大便利了我們管理k8s集羣。
這裏就介紹一下dashboard的部署。
部署
1:nodes節點上從阿里雲的docker倉庫下載Dashboard的相關鏡像。
# docker pull registry.cn-hangzhou.aliyuncs.com/capfgd/kubernetes-dashboard-amd64:v1.8.3
2:修改tag名稱。
# docker tag registry.cn-hangzhou.aliyuncs.com/capfgd/kubernetes-dashboard-amd64:v1.8.3 k8s.gcr.io/kubernetes-dashboard-amd64:v1.8.3
3:從官方網站上下載dashboard的yaml編排文件,並進行相應的修改。
kubernetes-dashboard.yaml文件的內容大概如下:
# Copyright 2017 The Kubernetes Authors.
#
# Licensed under the Apache License, Version 2.0 (the "License");
# you may not use this file except in compliance with the License.
# You may obtain a copy of the License at
#
# http://www.apache.org/licenses/LICENSE-2.0
#
# Unless required by applicable law or agreed to in writing, software
# distributed under the License is distributed on an "AS IS" BASIS,
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
# See the License for the specific language governing permissions and
# limitations under the License.
# Configuration to deploy release version of the Dashboard UI compatible with
# Kubernetes 1.8.
#
# Example usage: kubectl create -f <this_file>
# ------------------- Dashboard Secret ------------------- #
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1beta2
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: k8s.gcr.io/kubernetes-dashboard-amd64:v1.8.3
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
ports:
- port: 443
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard可以看到該文件創建了dashboard所需的相關資源,包括Secret、ServiceAccount、Role、RoleBinding、Deployment、Service。
其中ServiceACcount給訪問pod創建了一個用戶。
Secret這裏創建了一個空的Secret對象,Role和RoleBinding則是kubernets的RABC鑑權機制中的兩個對象,用於描述用戶和資源之間的連接權限。
Deployment定義了kubernetes-dashboard的pod信息。
Service則爲pod創建了一個訪問的入口,由於官方採用的是kubelet proxy的方式來訪問,這裏不做修改,當然,也可以通過NodePort方式來進行訪問dashboard。
當然,如果直接用官方提供的該文件創建dashboard,由於創建的用戶kubernetes-dashboard綁定的角色爲kubernetes-dashboard-minimal,由於改角色並沒有訪問和操作集羣的權限,因此登陸dashboard的時候,會提示權限錯誤:“configmaps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard"。因此需修改RoleBinding的相關參數,綁定權限更高的角色:
kind: ClusterRoleBinding apiVersion: rbac.authorization.k8s.io/v1beta1 metadata: name: kubernetes-dashboard subjects: - kind: ServiceAccount name: kubernetes-dashboard namespace: kube-system roleRef: kind: ClusterRole name: cluster-admin apiGroup: rbac.authorization.k8s.io
4:master上通過kubernetes-dashboard.yaml文件,創建dashboard:
# kubectl create -f kubernetes-dashboard.yaml secret "kubernetes-dashboard-certs" created serviceaccount "kubernetes-dashboard" created role.rbac.authorization.k8s.io "kubernetes-dashboard-minimal" created rolebinding.rbac.authorization.k8s.io "kubernetes-dashboard-minimal" created deployment.apps "kubernetes-dashboard" created service "kubernetes-dashboard" created
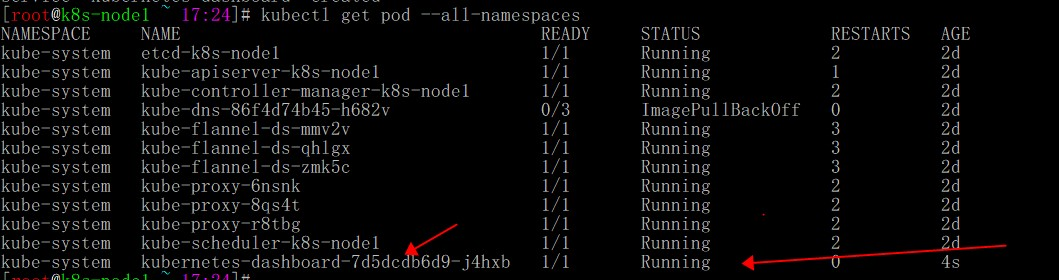
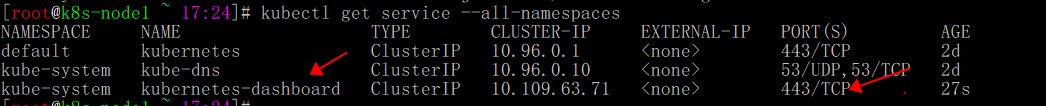
5:稍等一會,則可以看到k8s以及創建了相關的pod和service:
# kubectl get pod --all-namespaces # kubectl get service --all-namespaces
6:開啓kubelec proxy,開放dashboard端口,以便我們可以訪問ui頁面。(該方法爲官方推介的其中一種方法,也可以使用NodePort方式):
# kubectl proxy --address=192.168.232.130 --accept-hosts='^*$' &
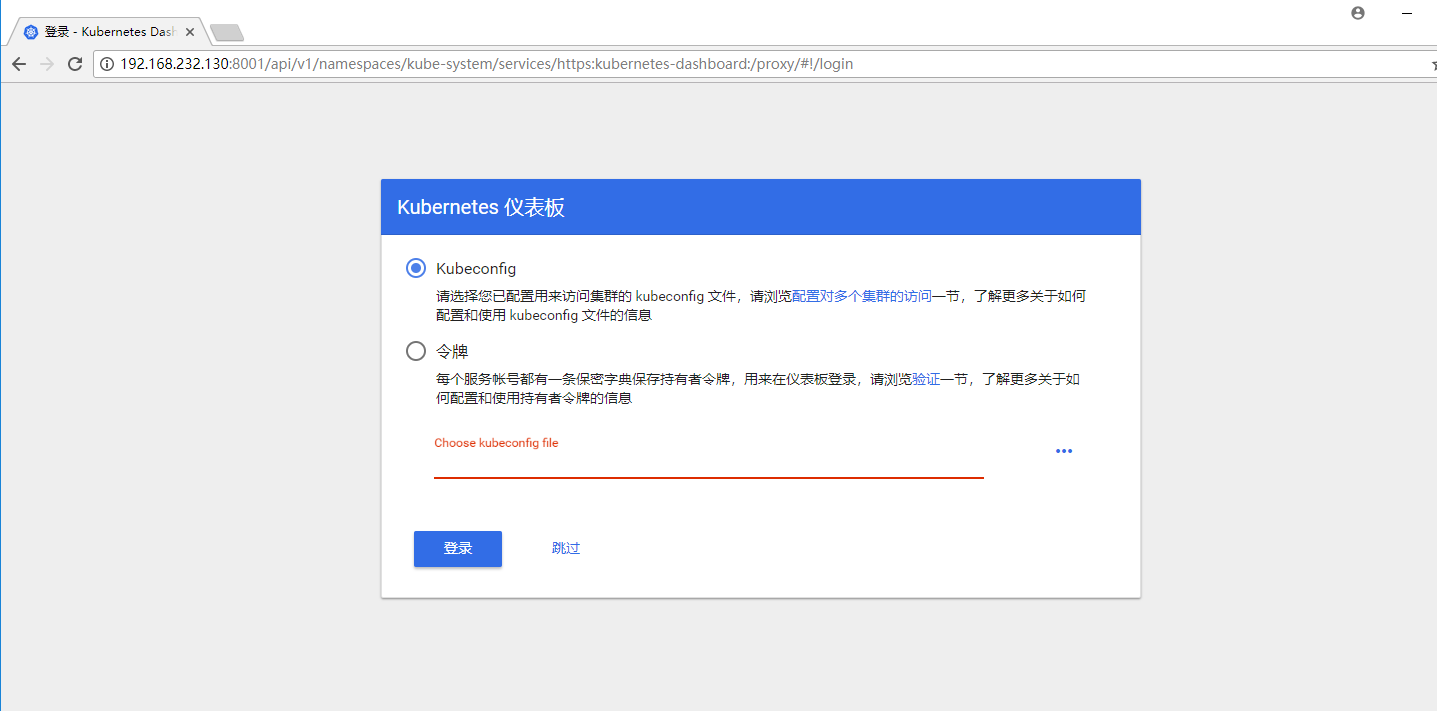
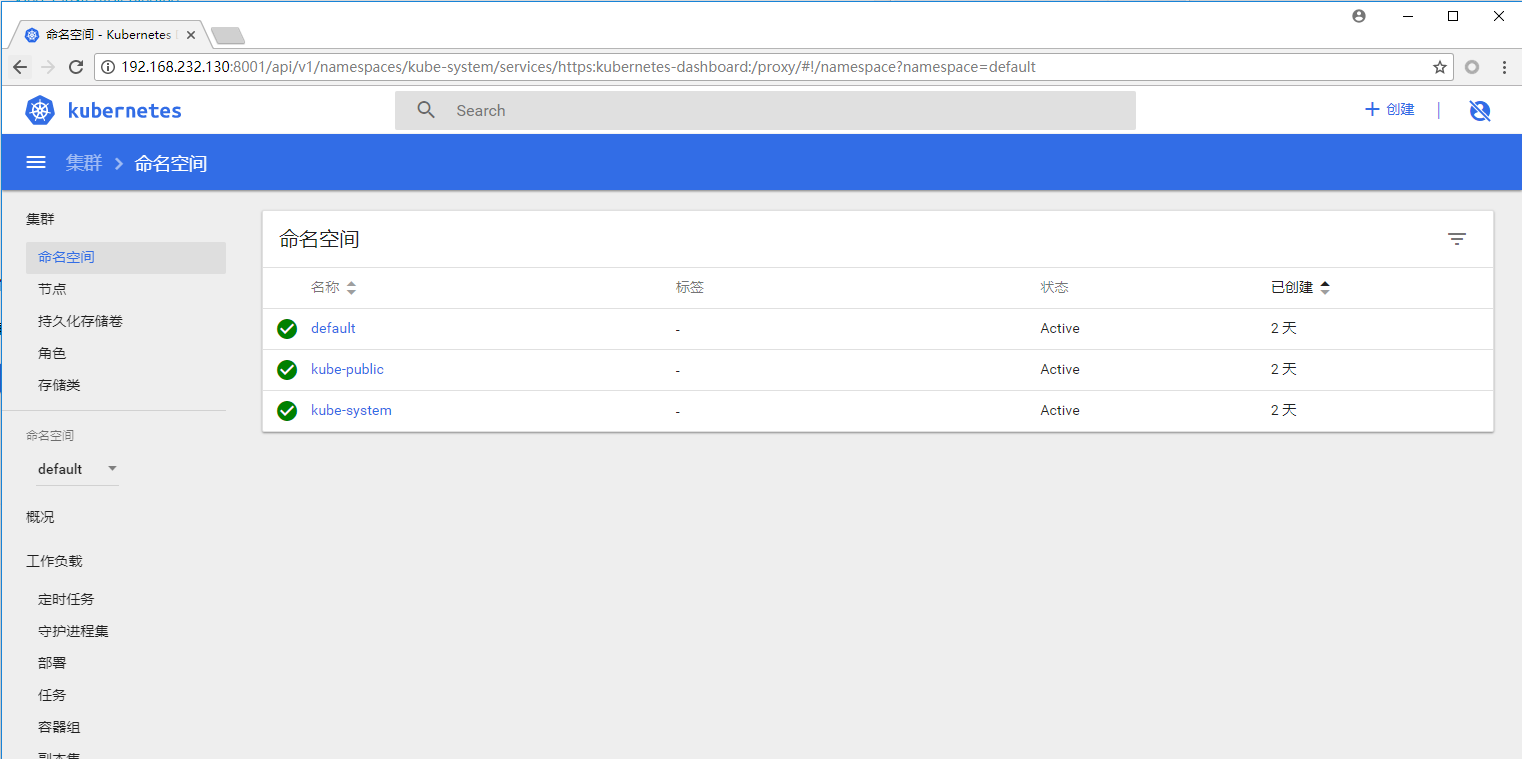
配置完之後使用http://192.168.232.130:8001/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxy/#!/overview?namespace=default訪問dashboard。
由於我們以及對用戶做過了相應的授權和綁定,因此可以直接選擇“跳過”來登陸。但該方法缺少了一些安全性,所以還是建議大家可以儘量使用token或者"用戶+密碼驗證"的方式來登陸dashboard。