實驗環境:
LDAP(輕量級目錄訪問協議)是一個能實現提供被稱爲目錄服務的信息服務,也是一套用戶認證體系系統;一般在大型企業、學校、政府單位使用的比較多,LDAP是由4部分組成,這4部分分別是slapd(獨立LDAP守護進程)、slurpd(獨立的LDAP更新複製守護進程)、LDAP協議庫、工具軟件和示例客戶端(phpLDAPadmin),目錄服務是一種特殊的數據庫系統,用來存儲用戶信息的數據庫,讀寫速度非常快,擴展性非常強,可以實現與地方系統直接對接整合起來統一管理用戶信息。

LDAP說起來也不簡單,但是ALDP在Linux應用範圍是比較廣泛的,如果想要深入的瞭解LDAP,建議去看下劉遄老師《Linux就該這麼學》這本教程,裏面解釋的非常詳細,也可以在百度輸入此書名去官網看,想要在Linux部署還是推薦這本書去系統的學習,對初學者還是很有版本的,這篇文章搭建ldap+phpldapadmin也是在Linux環境下運行的,所以還是需要Linux基礎才能看懂下面的配置步驟。
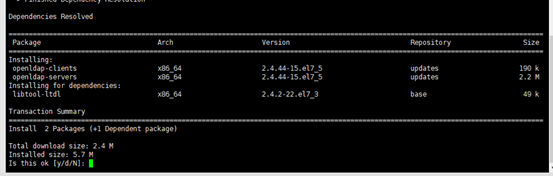
[root@centos7 ~]# yum install openldap-servers openldap-clients -y
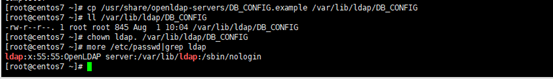
[root@centos7 ~]# cp /usr/share/openldap-servers/DB_CONFIG.example /var/lib/ldap/DB_CONFIG
[root@centos7 ~]# ll /var/lib/ldap/DB_CONFIG
-rw-r--r--. 1 root root 845 Aug 1 10:04 /var/lib/ldap/DB_CONFIG
[root@centos7 ~]# chown ldap. /var/lib/ldap/DB_CONFIG //授權配置文件
[root@centos7 ~]# more /etc/passwd|grep ldap
ldap:x:55:55:OpenLDAP server:/var/lib/ldap:/sbin/nologin
[root@centos7 ~]# systemctl start slapd.service //啓動slapd服務
[root@centos7 ~]# systemctl enable slapd.service //設置開機自動啓動slapd服務
{SSHA}d5pkA0TU6b+8/kEoMIxJ59QofCLV
[root@centos7 ~]# vim chrootpw.ldif
dn: olcDatabase={0}config,cn=config
olcRootPW: {SSHA}d5pkA0TU6b+8/kEokgQeMIxJ59QofCLV
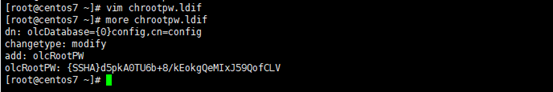
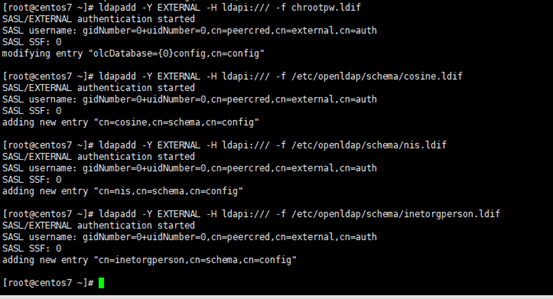
[root@centos7 ~]# ldapadd -Y EXTERNAL -H ldapi:/// -f chrootpw.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
modifying entry "olcDatabase={0}config,cn=config"
[root@centos7 ~]# ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/openldap/schema/cosine.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
adding new entry "cn=cosine,cn=schema,cn=config"
[root@centos7 ~]# ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/openldap/schema/nis.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
adding new entry "cn=nis,cn=schema,cn=config"
[root@centos7 ~]# ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/openldap/schema/inetorgperson.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
adding new entry "cn=inetorgperson,cn=schema,cn=config"
{SSHA}Oq61fgUFW9+ItZboTaW1+VbLuAYst7zw
注意:下面配置文件這裏得注意每一個屬性: 後必須有空格,但是值的後面不能有任何空格
[root@centos7 ~]# vim chdomain.ldif
# replace to your own domain name for "dc=***,dc=***" section
# specify the password generated above for "olcRootPW" section
dn: olcDatabase={1}monitor,cn=config
olcAccess: {0}to * by dn.base="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth"
read by dn.base="cn=Manager,dc=srv,dc=world" read by * none
dn: olcDatabase={2}hdb,cn=config
dn: olcDatabase={2}hdb,cn=config
olcRootDN: cn=Manager,dc=srv,dc=world
dn: olcDatabase={2}hdb,cn=config
olcRootPW: {SSHA}Oq61fgUFW9+ItZboTaW1+VbLuAYst7zw
dn: olcDatabase={2}hdb,cn=config
olcAccess: {0}to attrs=userPassword,shadowLastChange by
dn="cn=Manager,dc=srv,dc=world" write by anonymous auth by self write by * none
olcAccess: {1}to dn.base="" by * read
olcAccess: {2}to * by dn="cn=Manager,dc=srv,dc=world" write by * read
[root@centos7 ~]# ldapmodify -Y EXTERNAL -H ldapi:/// -f chdomain.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
modifying entry "olcDatabase={1}monitor,cn=config"
modifying entry "olcDatabase={2}hdb,cn=config"
modifying entry "olcDatabase={2}hdb,cn=config"
modifying entry "olcDatabase={2}hdb,cn=config"
modifying entry "olcDatabase={2}hdb,cn=config"
[root@centos7 ~]# vim basedomain.ldif
# replace to your own domain name for "dc=***,dc=***" section
dn: cn=Manager,dc=srv,dc=world
objectClass: organizationalRole
description: Directory Manager
objectClass: organizationalUnit
objectClass: organizationalUnit
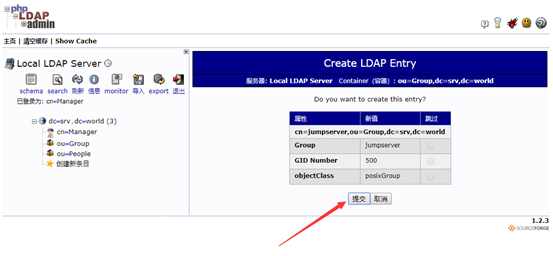
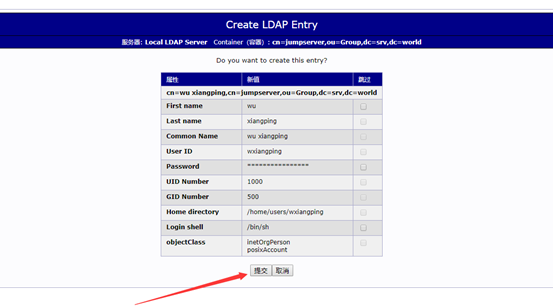
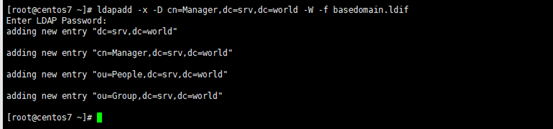
[root@centos7 ~]# ldapadd -x -D "cn=Manager,dc=srv,dc=world" -W -f basedomain.ldif
Enter LDAP Password: //輸入上面設置的目錄管理器密碼 password
adding new entry "dc=srv,dc=world"
adding new entry "cn=Manager,dc=srv,dc=world"
adding new entry "ou=People,dc=srv,dc=world"
adding new entry "ou=Group,dc=srv,dc=world"
[root@centos7 ~]# ldapsearch -x -b "cn=Manager,dc=srv,dc=world"
# base <cn=Manager,dc=srv,dc=world> with scope subtree
dn: cn=Manager,dc=srv,dc=world
objectClass: organizationalRole
description: Directory Manager
[root@centos7 ~]# firewall-cmd --add-service=ldap --permanent
[root@centos7 ~]# firewall-cmd --reload
[root@centos7 ~]# yum install httpd-devel.x86_64 httpd.x86_64 -y
[root@centos7 ~]# mv /etc/httpd/conf.d/welcome.conf /etc/httpd/conf.d/welcome.conf.bak
[root@centos7 ~]# vim /etc/httpd/conf/httpd.conf
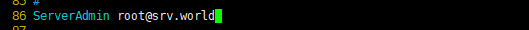
# line 86: change to admin's email address
ServerAdmin [email protected]
# line 95: change to your server's name
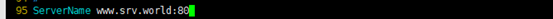
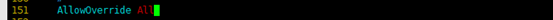
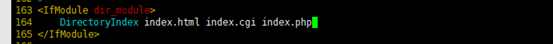
# line 164: add file name that it can access only with directory's name
DirectoryIndex index.html index.cgi index.php
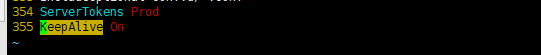
# add follows to the end //在尾部新增
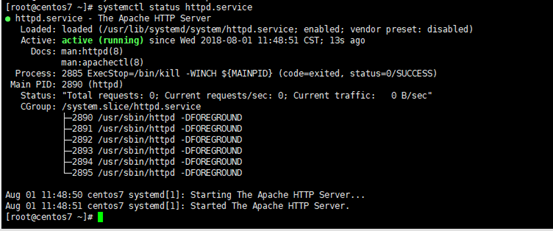
[root@centos7 ~]# systemctl start httpd.service
[root@centos7 ~]# systemctl enable httpd.service
[root@centos7 ~]# firewall-cmd --add-service=http --permanent //防火牆排除httpd服務,如果沒有啓用防火牆,此步驟可以忽略。
[root@centos7 ~]# firewall-cmd --reload //重新加載firewall
[root@centos7 ~]# vim /var/www/html/index.html //測試apache服務
<div style="width: 100%; font-size: 40px; font-weight: bold; text-align: center;">
測試:http://192.168.3.41/index.html
[root@centos7 ~]# yum -y install php php-mbstring php-pear
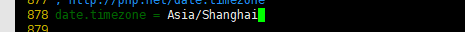
[root@centos7 ~]# vim /etc/php.ini
[root@centos7 ~]# systemctl restart httpd.service
[root@centos7 ~]# vim /var/www/html/index.php
<div style="width: 100%; font-size: 40px; font-weight: bold; text-align: center;">
測試:http://192.168.3.41/index.php
可以不安裝phpLDAPadmin工具,直接下載Windows系統下的LdapAdmin應用程序
[root@centos7 ~]# yum install phpldapadmin.noarch -y
[root@centos7 ~]# vim /etc/phpldapadmin/config.php
397 $servers->setValue('login','attr','dn'); #取消397行註釋
398 //$servers->setValue('login','attr','uid'); #註釋398
[root@centos7 ~]# vim /etc/httpd/conf.d/phpldapadmin.conf
# Web-based tool for managing LDAP servers
Alias /phpldapadmin /usr/share/phpldapadmin/htdocs
Alias /ldapadmin /usr/share/phpldapadmin/htdocs
<Directory /usr/share/phpldapadmin/htdocs>
[root@centos7 ~]# systemctl restart httpd.service
[root@centos7 ~]# systemctl status httpd.service
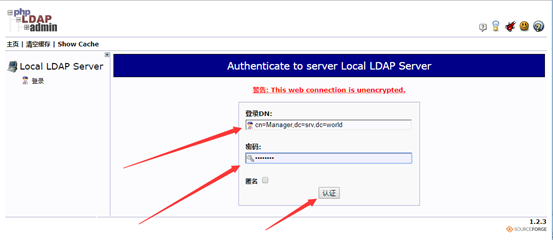
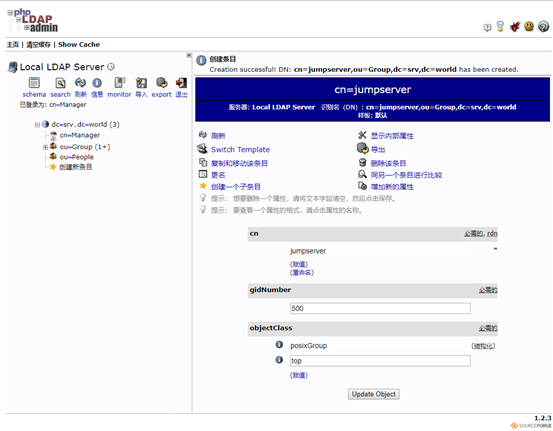
測試:http://192.168.3.41/ldapadmin/

[root@centos7 ~]# setsebool -P httpd_can_connect_ldap on
9.3、phpldapadmin的網站的apache配置文件
# vim /etc/httpd/conf.d/phpldapadmin.conf
# Web-based tool for managing LDAP servers
Alias /phpldapadmin /usr/share/phpldapadmin/htdocs
Alias /ldapadmin /usr/share/phpldapadmin/htdocs
#注意:/usr/share/phpldapadmin/htdocs 是phpldapadmin根目錄
<Directory /usr/share/phpldapadmin/htdocs>
這裏可以直接訪問phpldapadmin後臺,最好是通過apache做密碼驗證才能登錄,這樣比較安全。
參考文獻:httpd配置認證才能訪問網站(原創實踐操作).note
# vim /root/ldap_disable_bind_anon.ldif
dn: olcDatabase={-1}frontend,cn=config
[root@centos7 ~]# ldapadd -Y EXTERNAL -H ldapi:/// -f ldap_disable_bind_anon.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth