構建私有的 CA 機構
1、CA 介紹
CA(Certificate Authority)證書頒發機構主要負責證書的頒發、管理以及歸檔和吊銷。證書內包含了擁有證書者的姓名、地址、電子郵件帳號、公鑰、證書有效期、發放證書的CA、CA的數字簽名等信息。證書主要有三大功能:加密、簽名、身份驗證。爲什麼要構建私有CA?
因爲公共 CA (比如排名前幾的這幾家:Comodo, Symantec, GlobalSign, DigiCert, StartCom)頒發證書要收費,而且價格很貴。當然現在也有了像 Letsencrypt 這樣的免費 CA。 我們的應用是企業內網,域名使用私有域名,沒有辦法使用互聯網的 CA 辦法的證書。
環境:server:192.168.11.12 node1:192.168.11.132、構建私有 CA
1)、檢查安裝 openssl
rpm -qa openssl如果未安裝,則安裝 openssl
yum install openssl openssl-devel2)、查看配置文件
openssl 配置/etc/pki/tls/openssl.cnf有關CA的配置。如果服務器爲證書籤署者的身份那麼就會用到此配置文件,此配置文件對於證書申請者是無作用的。
####################################################################
[ ca ]
default_ca = CA_default # 默認的CA配置;CA_default指向下面配置塊
####################################################################
[ CA_default ]
dir = /etc/pki/CA # CA的默認工作目錄
certs = $dir/certs # 認證證書的目錄
crl_dir = $dir/crl # 證書吊銷列表的路徑
database = $dir/index.txt # 數據庫的索引文件
new_certs_dir = $dir/newcerts # 新頒發證書的默認路徑
certificate = $dir/cacert.pem # 此服務認證證書,如果此服務器爲根CA那麼這裏爲自頒發證書
serial = $dir/serial # 下一個證書的證書編號
crlnumber = $dir/crlnumber # 下一個吊銷的證書編號
crl = $dir/crl.pem # The current CRL
private_key = $dir/private/cakey.pem# CA的私鑰
RANDFILE = $dir/private/.rand # 隨機數文件
x509_extensions = usr_cert # The extentions to add to the cert
name_opt = ca_default # 命名方式,以ca_default定義爲準
cert_opt = ca_default # 證書參數,以ca_default定義爲準
default_days = 365 # 證書默認有效期
default_crl_days= 30 # CRl的有效期
default_md = sha256 # 加密算法
preserve = no # keep passed DN ordering
policy = policy_match #policy_match策略生效
# For the CA policy
[ policy_match ]
countryName = match #國家;match表示申請者的申請信息必須與此一致
stateOrProvinceName = match #州、省
organizationName = match #組織名、公司名
organizationalUnitName = optional #部門名稱;optional表示申請者可以的信息與此可以不一致
commonName = supplied
emailAddress = optional
# For the 'anything' policy
# At this point in time, you must list all acceptable 'object'
# types.
[ policy_anything ] #由於定義了policy_match策略生效,所以此策略暫未生效
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional3)、根證書服務器目錄
根CA服務器:因爲只有 CA 服務器的角色,所以用到的目錄只有/etc/pki/CA
網站服務器:只是證書申請者的角色,所以用到的目錄只有/etc/pki/tls
4)、創建所需要的文件
[root@server ~]# cd /etc/pki/CA/
[root@server CA]# ls
certs crl newcerts private
[root@server CA]# touch index.txt #生成證書索引數據庫文件
[root@server CA]# ls
certs crl index.txt newcerts private
[root@server CA]# echo 01 > serial #指定第一個頒發證書的序列號
[root@server CA]# ls
certs crl index.txt newcerts private serial5)、創建密鑰
在根CA服務器上創建密鑰,密鑰的位置必須爲/etc/pki/CA/private/cakey.pem,這個是openssl.cnf中中指定的路徑,只要與配置文件中指定的匹配即可。
[root@server CA]# (umask 066; openssl genrsa -out private/cakey.pem 2048)
Generating RSA private key, 2048 bit long modulus
........................................................+++
.........................+++
e is 65537 (0x10001)6)、生成自簽名證書
根CA自簽名證書,根CA是最頂級的認證機構,沒有人能夠認證他,所以只能自己認證自己生成自簽名證書。
[root@server CA]# openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -days 7300 -out /etc/pki/CA/cacert.pem -days 7300
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:BEIJING
Locality Name (eg, city) [Default City]:BEIJING
Organization Name (eg, company) [Default Company Ltd]:CA
Organizational Unit Name (eg, section) []:OPT
Common Name (eg, your name or your server's hostname) []:ca.qf.com
Email Address []:
[root@server CA]# ls
cacert.pem certs crl index.txt newcerts private serial-new: 生成新證書籤署請求
-x509: 專用於CA生成自簽證書
-key: 生成請求時用到的私鑰文件
-days n: 證書的有效期限
-out /PATH/TO/SOMECERTFILE: 證書的保存路徑7)、下載安裝證書
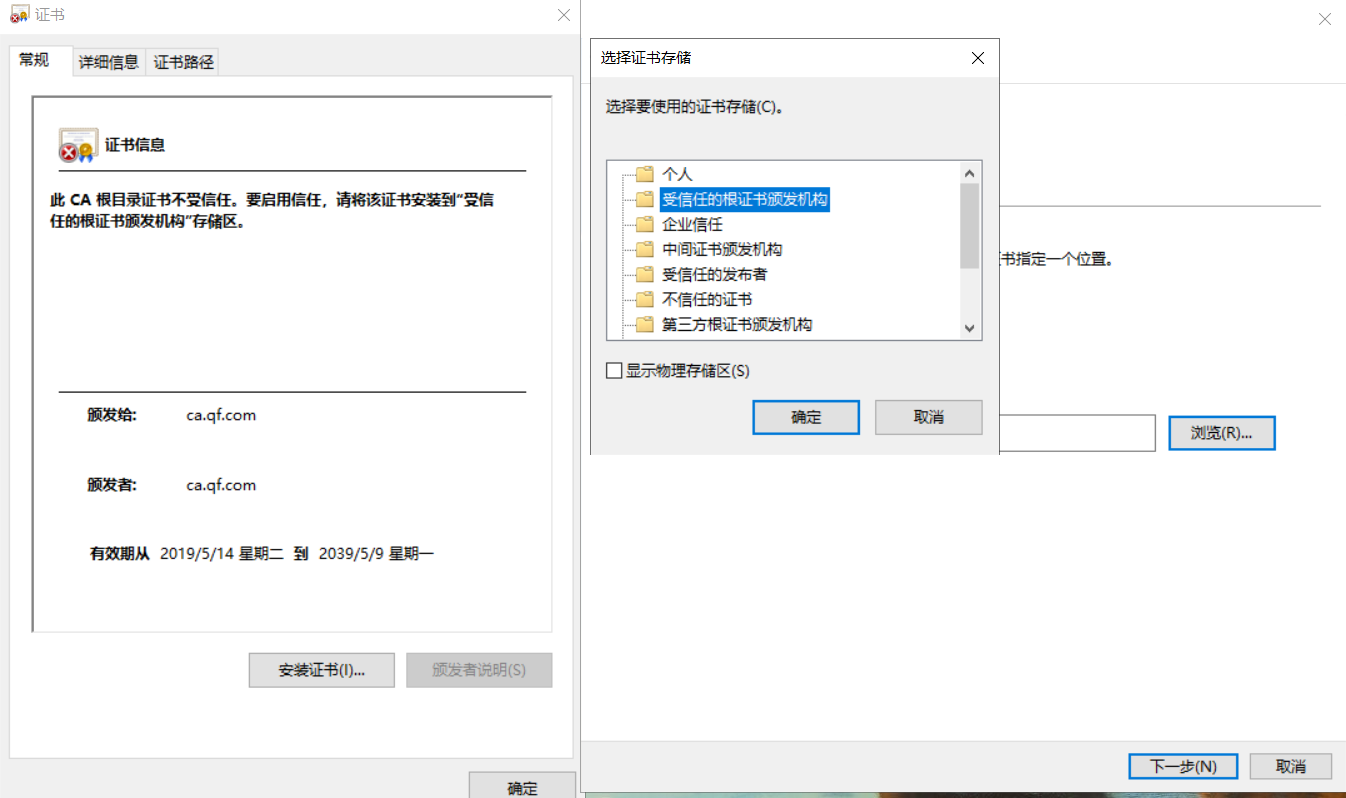
/etc/pki/CA/cacert.pem就是生成的自簽名證書文件,使用 SZ/xftp工具將他導出到窗口機器中。然後雙擊安裝此證書到受信任的根證書頒發機構
或:將/etc/pki/CA/cacert.pem 傳到Windows上,看一下 sz /etc/pki/CA/cacert.pem
在Windows上接收並更改後綴名爲 .cer
3、CA 證書申請及簽名
1)、檢查安裝 openssl
rpm -qa openssl如果未安裝,則安裝 openssl
yum install openssl openssl-devel2)、客戶端生成私鑰文件
[root@node1 ~]# (umask 066; openssl genrsa -out /etc/pki/tls/private/www.qf.com.key 2048)
Generating RSA private key, 2048 bit long modulus
......................+++
....................................................................................+++
e is 65537 (0x10001)
[root@node1 ~]# cd /etc/pki/tls/private
[root@node1 private]# ls
www.qf.com.key3)、客戶端用私鑰加密生成證書請求
[root@node1 private]# ls ../
cert.pem certs misc openssl.cnf private
[root@node1 private]# openssl req -new -key /etc/pki/tls/private/www.qf.com.key -days 365 -out /etc/pki/tls/www.qf.com.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:BEIJING
Locality Name (eg, city) [Default City]:BEIJING
Organization Name (eg, company) [Default Company Ltd]:QF
Organizational Unit Name (eg, section) []:OPT
Common Name (eg, your name or your server's hostname) []:www.qf.com
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
[root@node1 private]# cd ../
[root@node1 tls]# ls
cert.pem certs misc openssl.cnf private www.qf.com.csrCSR(Certificate Signing Request)包含了公鑰和名字信息。通常以.csr爲後綴,是網站向CA發起認證請求的文件,是中間文件。
在這一命令執行的過程中,系統會要求填寫如下信息:
| 要求添寫的內容 | |
|---|---|
| Country Name (2 letter code) | 使用國際標準組織(ISO)國碼格式,填寫2個字母的國家代號。中國請填寫CN |
| State or Province Name (full name) | 省份,比如填寫BeiJing |
| Locality Name (eg, city) | 城市,比如填寫BeiJing |
| Organization Name (eg, company) | 組織單位,比如填寫公司名稱的拼音 |
| Organizational Unit Name (eg, section) | 比如填寫IT Dept |
| Common Name (eg, your websites domain name) | 城市,比如填寫BeiJing |
| Email Address | 郵件地址,可以不填 |
| A challenge password | 可以不填 |
| An optional company name | 可以不填 |
最後把生成的請求文件(/etc/pki/tls/www.qf.com.csr)傳輸給CA ,這裏我使用scp命令,通過ssh協議,將該文件傳輸到CA下的/etc/pki/CA/private/目錄
root@node1 tls]# scp www.qf.com.csr 192.168.11.13:/etc/pki/CA/private/
[email protected]'s password:
www.qf.com.csr 100% 997 777.2KB/s 00:00 4、CA 簽署證書
[root@server ~]# openssl ca -in /etc/pki/CA/private/www.qf.com.csr -out
/etc/pki/CA/certs/www.qf.com.ctr -days 365
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Mar 14 13:45:02 2019 GMT
Not After : Mar 13 13:45:02 2020 GMT
Subject:
countryName = CN
stateOrProvinceName = BEIJING
organizationName = QF
organizationalUnitName = OPT
commonName = www.qf.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
08:65:70:98:2B:0B:15:D0:74:FE:69:58:05:B8:02:BC:45:D8:23:9B
X509v3 Authority Key Identifier:
keyid:60:6B:BC:F1:A1:01:BF:72:FD:7D:02:A8:BD:15:BE:9C:3B:3E:03:30
Certificate is to be certified until Mar 13 13:45:02 2020 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
證書通常以.crt爲後綴,表示證書文件
1、可能遇到的問題
[root@server ~]# openssl openssl ca -in /etc/pki/CA/private/www.qf.com.csr -out /etc/pki/CA/certs/www.qf.com.ctr -days 365
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
The organizationName field needed to be the same in the
CA certificate (CA) and the request (QF)因爲默認使用/etc/pki/tls/openssl.cnf,裏面要求其一致,修改organizationName=supplied
修改 /etc/pki/tls/openssl.cnf
# For the CA policy
[ policy_match ]
countryName = match
stateOrProvinceName = match
organizationName = supplied
organizationalUnitName = optional
commonName = supplied
emailAddress = optional2、查看生成的證書的信息
[root@server ~]# openssl x509 -in /etc/pki/CA/certs/www.qf.com.ctr -noout -subject
subject= /C=CN/ST=BEIJING/O=QF/OU=OPT/CN=www.qf.com3、將生成的證書發放給請求客戶端
[root@server ~]# scp www.qf.com.ctr [email protected]:/etc/pki/CA/certs/
[email protected]'s password:
www.qf.com.ctr 100% 4422 1.3MB/s 00:00 4、CA吊銷證書
1)、知道客戶端吊銷的證書的serial
[root@server ~]#openssl x509 -in /PATH/FROM/CERT_FILE -noout -serial -subject2)、吊銷證書
先根據客戶提交的serial與subject信息,對比檢驗是否與index.txt文件中的信息一致;然後
[root@server ~]#openssl ca -revoke /etc/pki/CA/newcerts/SERIAL.pem3)、生成吊銷證書的編號
第一次吊銷一個證書時才需要執行
[root@server ~]#echo 01 > /etc/pki/CA/crlnumber4)、更新證書吊銷列表
[root@server ~]#openssl ca -gencrl -out thisca.crl5)、查看證書吊銷列表
[root@server ~]#openssl crl -in /PATH/FROM/CRL_FILE.crl -noout -text