-
關於防火牆基礎配置可參考博文:保證Linux系統安全之CentOS 7 firewalld防火牆入門詳解
- 關於防火牆IP僞裝和端口轉發可參考博文:保證Linux系統安全之firewalld防火牆配置地址僞裝和端口轉發詳解
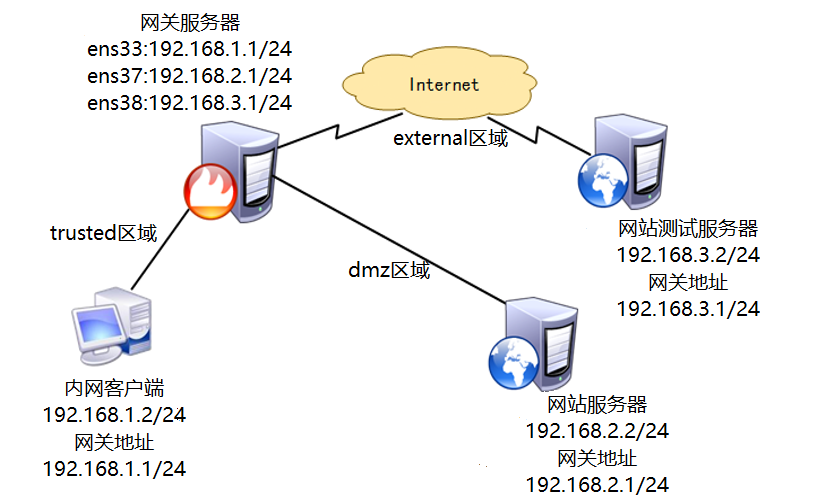
案例環境:
需求描述:
- 連接內網網卡ens33地址爲192.168.1.1,分配到firewall的trusted區域;
連接服務器網卡ens37地址爲192.168.2.1,分配到firewall的dmz區域;
網關服務器連接互聯網網卡ens38地址爲192.168.3.1,爲公網IP地址,分配到firewall的external區域;- 網站服務器和網關服務器均通過SSH來遠程管理,爲了安全,將SSH默認端口改爲12345;
- 網站服務器開啓 HTTPS,過濾未加密的HTTP流量;
- 網站務器拒絕ping測試,網關服務器拒絕來自互聯網上的ping測試;
- 公司內網用戶需要通過網關服務器共享上網;
- 互聯網用戶需要訪問網站服務器;
操作步驟
- 基本環境配置;
- DMZ網站服務器環境搭建並啓動服務;
- DMZ網站服務器上啓動並配置firewalld防火牆策略;
- Internet測試網站環境搭建並啓動服務、設置防火牆規則;
- 網關服務器配置firewalld策略;
- 配置IP僞裝與端口轉發;
案例實施
1.基本環境配置
(1)確認網關服務器地址
[root@localhost ~]# ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.1 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::46cb:a832:aea4:7b65 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:00:11:89 txqueuelen 1000 (Ethernet)
RX packets 158 bytes 46815 (45.7 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 31 bytes 4270 (4.1 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@localhost ~]# ifconfig ens37
ens37: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.2.1 netmask 255.255.255.0 broadcast 192.168.2.255
inet6 fe80::8e69:6ed5:da33:fda4 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:00:11:93 txqueuelen 1000 (Ethernet)
RX packets 104 bytes 27490 (26.8 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 189 bytes 31923 (31.1 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@localhost ~]# ifconfig ens38
ens38: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.1 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::5348:53e2:b3bc:d35b prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:00:11:9d txqueuelen 1000 (Ethernet)
RX packets 101 bytes 27238 (26.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 188 bytes 31304 (30.5 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0(2)網關服務器開啓路由功能
[root@localhost ~]# vim /etc/sysctl.conf
……………… //省略部分內容,添加以下內容
net.ipv4.ip_forward = 1
[root@localhost ~]# sysctl -p
net.ipv4.ip_forward = 1(3)配置DMZ區域網站服務器地址、網關
[root@localhost ~]# ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.2.2 netmask 255.255.255.0 broadcast 192.168.2.255
inet6 fe80::8744:c79c:521f:823f prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:2b:56:b5 txqueuelen 1000 (Ethernet)
RX packets 114 bytes 34398 (33.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 30 bytes 4162 (4.0 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@localhost ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.2.1 0.0.0.0 UG 100 0 0 ens33(4)配置Internet測試網站服務器IP地址、網關
[root@localhost ~]# ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.2 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::7c8b:1ec0:7e4d:ac6 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:98:41:ac txqueuelen 1000 (Ethernet)
RX packets 113 bytes 31388 (30.6 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 40 bytes 4541 (4.4 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@localhost ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.3.1 0.0.0.0 UG 100 0 0 ens33(5)配置內部客戶機IP地址、網關
[root@localhost ~]# ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.2 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::9bb5:2c48:1095:d75a prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:fb:76:60 txqueuelen 1000 (Ethernet)
RX packets 106 bytes 29223 (28.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 31 bytes 4349 (4.2 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@localhost ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.1.1 0.0.0.0 UG 100 0 0 ens332.DMZ網站服務器環境並啓動服務
(1)開啓firewalld防火牆
[root@localhost ~]# systemctl start firewalld(2)搭建httpd服務
[root@localhost ~]# yum -y install httpd
//基於http訪問的HTTP網站
[root@localhost ~]# yum -y install httpd mod_ssl
//基於https訪問的HTTP網站
[root@localhost ~]# systemctl start httpd
//開啓HTTP服務(3)更改SSH的監聽端口(重啓服務時建議關閉SELinux)
[root@localhost ~]# vim /etc/ssh/sshd_config
………… //省略部分內容,修改以下內容
Port 12345
[root@localhost ~]# setenforce 0
//臨時關閉SELinux
[root@localhost ~]# systemctl restart sshd
//重啓ssh服務3.DMZ網站服務器上啓動並配置firewalld防火牆策略
(1)設置防火牆默認區域爲dmz區域
[root@localhost ~]# firewall-cmd --set-default-zone=dmz
success(2)爲dmz區域添加相應服務及端口
[root@localhost ~]# firewall-cmd --zone=dmz --add-service=https
success
[root@localhost ~]# firewall-cmd --zone=dmz --add-port=12345/tcp
success(3)禁止ping測試
[root@localhost ~]# firewall-cmd --zone=dmz --add-icmp-block=echo-request
success(4)將默認的ssh服務刪除
[root@localhost ~]# firewall-cmd --zone=dmz --remove-service=ssh
success(5)保存當前防火牆配置
[root@localhost ~]# firewall-cmd --runtime-to-permanent
success
//將臨時配置轉換爲永久配置
[root@localhost ~]# firewall-cmd --list-all --zone=dmz
//查看並確認配置信息
dmz (active)
target: default
icmp-block-inversion: no
interfaces: ens33
sources:
services: https
ports: 12345/tcp
protocols:
masquerade: no
forward-ports:
sourceports:
icmp-blocks: echo-request
rich rules: 4. Internet測試網站環境搭建並啓動服務、設置防火牆規則
搭建方法可參考第2、3步
5. 網關服務器配置firewalld策略
(1)開啓防火牆
[root@localhost ~]# systemctl start firewalld(2)設置默認區域爲externel區域
[root@localhost ~]# firewall-cmd --set-default-zone=external
success(3)將各個網卡分配至指定區域
[root@localhost ~]# firewall-cmd --change-interface=ens33 --zone=trusted
success
[root@localhost ~]# firewall-cmd --change-interface=ens37 --zone=dmz
success(4)內部客戶機訪問DMZ網站測試
[root@localhost ~]# firewall-cmd --runtime-to-permanent
success
[root@localhost ~]# firewall-cmd --get-active-zones
dmz
interfaces: ens37
external
interfaces: ens38
trusted
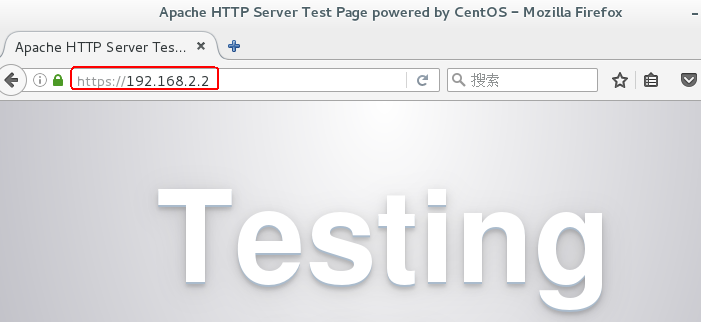
interfaces: ens33(5)內部客戶機訪問網站服務器
(6)更改ssh服務監聽端口
[root@localhost ~]# vim /etc/ssh/sshd_config
………… //省略部分內容,修改以下內容
Port 12345
[root@localhost ~]# setenforce 0
//臨時關閉SELinux
[root@localhost ~]# systemctl restart sshd
//重啓ssh服務(7)配置external區域添加TCP的12345端口、移除ssh服務
[root@localhost ~]# firewall-cmd --zone=external --add-port=12345/tcp
success
[root@localhost ~]# firewall-cmd --zone=external --remove-service=ssh
success(8)配置external區域進行ping測試、保存爲永久配置
[root@localhost ~]# firewall-cmd --zone=external --add-icmp-block=echo-request
success
[root@localhost ~]# firewall-cmd --runtime-to-permanent
success(9)Internet測試服務器遠程網關服務器
[root@localhost ~]# ssh -p 12345 192.168.3.1
The authenticity of host '[192.168.3.1]:12345 ([192.168.3.1]:12345)' can't be established.
ECDSA key fingerprint is b2:4e:e8:f9:23:9f:85:dc:54:87:97:eb:15:cc:b0:48.
Are you sure you want to continue connecting (yes/no)? (10)內部客戶機遠程DMZ網站服務器
[root@localhost ~]# ssh -p 12345 192.168.2.2
The authenticity of host '[192.168.2.2]:12345 ([192.168.2.2]:12345)' can't be established.
ECDSA key fingerprint is 25:54:5c:d5:ce:e1:04:9f:25:19:be:73:ce:93:86:54.
Are you sure you want to continue connecting (yes/no)? 6.網關服務器上配置IP轉發與端口轉發
默認external區域有IP轉發功能!
(1)刪除external區域中的IP僞裝,並利用富規則開啓
[root@localhost ~]# firewall-cmd --remove-masquerade --zone=external
success
[root@localhost ~]# firewall-cmd --zone=external --add-rich-rule='rule family=ipv4 source address=192.168.1.0/24 masquerade'
success(2)dmz網站服務器測試訪問Internet測試網站
(3)配置端口轉發實現Internet測試網站訪問dmz區域網站服務器(直接規則)
[root@localhost ~]# firewall-cmd --zone=external --add-forward-port=port=443:proto=tcp:toaddr=192.168.2.2
success
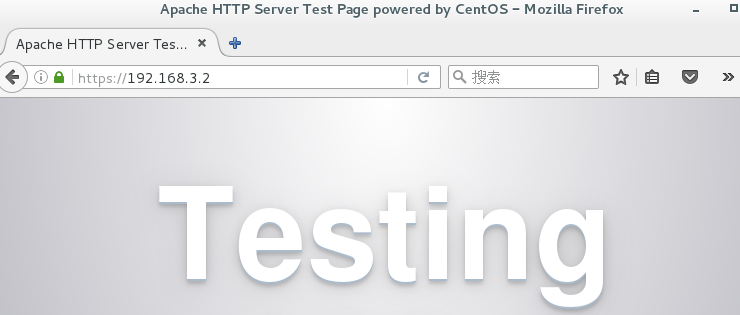
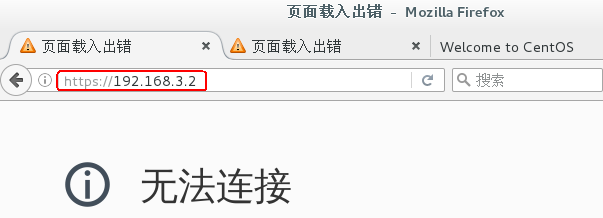
//網關服務器將互聯網測試機的請求轉發到dmz區域網站服務器(4)測試
(5)配置端口轉發實現Internet測試網站訪問dmz區域網站服務器(富規則)
需在ens38網卡上配置一個臨時IP地址
[root@localhost ~]# firewall-cmd --zone=external --add-rich-rule='rule family=ipv4 destination address=192.168.3.100 forward-port port=443 protocol=tcp to-addr=192.168.2.2'
success