本文介紹node節點的二進制部署過程。
一、軟件包下載地址
Node包:https://dl.k8s.io/v1.9.6/kubernetes-node-linux-amd64.tar.gz
# tar -zxvpf kubernetes-node-linux-amd64.tar.gz
# mv kubernetes/node/bin/kube* /usr/local/sbin/二、在master上創建kubelet-bootstrap 用戶並綁定system:node-bootstrapper 角色
kubelet 啓動時向 kube-apiserver 發送 TLS bootstrapping 請求,需要先將 bootstrap token 文件中的 kubelet-bootstrap 用戶賦予 system:node-bootstrapper 角色,然後 kubelet 纔有權限創建認證請求(certificatesigningrequests)。-user=kubelet-bootstrap 是前文master節點上文件 /etc/kubernetes/token.csv 中指定的用戶名
在master節點上運行:
# kubectl create clusterrolebinding kubelet-bootstrap \
--clusterrole=system:node-bootstrapper \
--user=kubelet-bootstrap
clusterrolebinding "kubelet-bootstrap" created三、node節點上設置kubelet
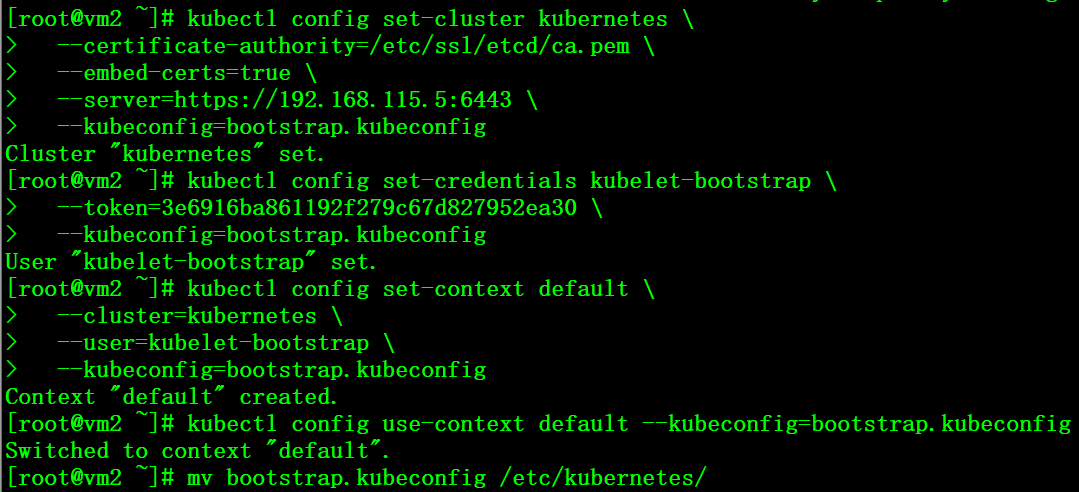
1、設置集羣參數
# kubectl config set-cluster kubernetes \
--certificate-authority=/etc/ssl/etcd/ca.pem \
--embed-certs=true \
--server=https://192.168.115.5:6443 \
--kubeconfig=bootstrap.kubeconfig2、設置客戶端認證參數,token同樣來自前文master節點上文件 /etc/kubernetes/token.csv
# kubectl config set-credentials kubelet-bootstrap \
--token=3e6916ba861192f279c67d827952ea30 \
--kubeconfig=bootstrap.kubeconfig3、設置上下文參數
# kubectl config set-context default \
--cluster=kubernetes \
--user=kubelet-bootstrap \
--kubeconfig=bootstrap.kubeconfig4、設置默認上下文
# kubectl config use-context default --kubeconfig=bootstrap.kubeconfig
# mv bootstrap.kubeconfig /etc/kubernetes/
5、創建工作目錄
# mkdir /var/lib/kubelet6、配置kubelet啓動腳本
# cat /usr/lib/systemd/system/kubelet.service
[Unit]
Description=Kubernetes Kubelet
Documentation=https://github.com/GoogleCloudPlatform/kubernetes
After=docker.service
Requires=docker.service
[Service]
WorkingDirectory=/var/lib/kubelet
ExecStart=/usr/local/sbin/kubelet \
--address=192.168.115.6 \
--hostname-override=192.168.115.6 \
--pod-infra-container-image=gcr.io/google_containers/pause-amd64:3.0 \
--experimental-bootstrap-kubeconfig=/etc/kubernetes/bootstrap.kubeconfig \
--kubeconfig=/etc/kubernetes/kubelet.kubeconfig \
--cert-dir=/etc/ssl/kubernetes \
--cluster-dns=10.254.0.2\
--cluster-domain=cluster.local. \
--hairpin-mode promiscuous-bridge \
--allow-privileged=true \
--serialize-image-pulls=false \
--logtostderr=true \
--v=2
ExecStartPost=/sbin/iptables -A INPUT -s 10.0.0.0/8 -p tcp --dport 4194 -j ACCEPT
ExecStartPost=/sbin/iptables -A INPUT -s 172.16.0.0/12 -p tcp --dport 4194 -j ACCEPT
ExecStartPost=/sbin/iptables -A INPUT -s 192.168.0.0/16 -p tcp --dport 4194 -j ACCEPT
ExecStartPost=/sbin/iptables -A INPUT -p tcp --dport 4194 -j DROP
Restart=on-failure
RestartSec=5
[Install]
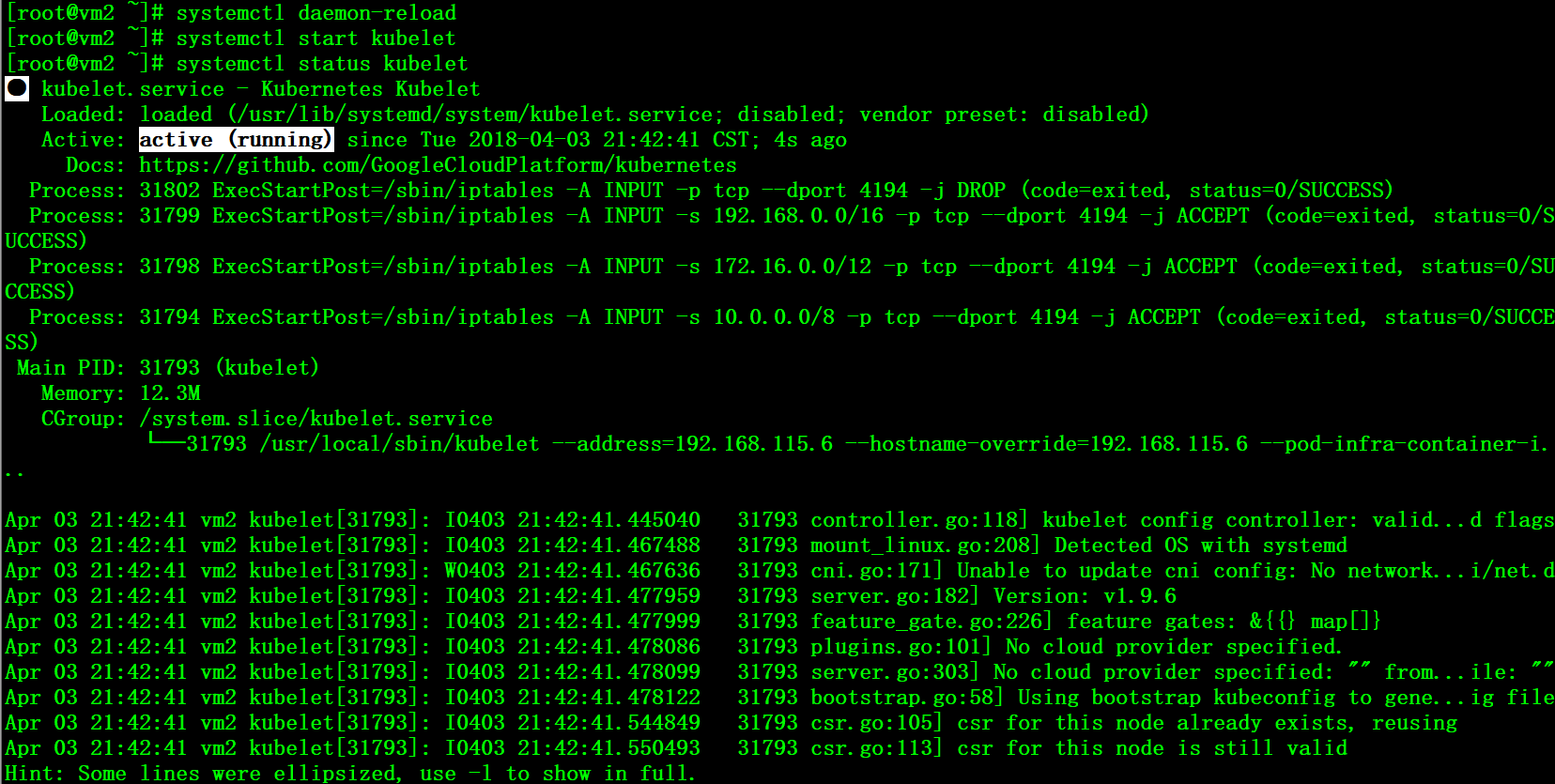
WantedBy=multi-user.target7、啓動測試
# systemctl daemon-reload
# systemctl start kubelet
# systemctl status kubelet
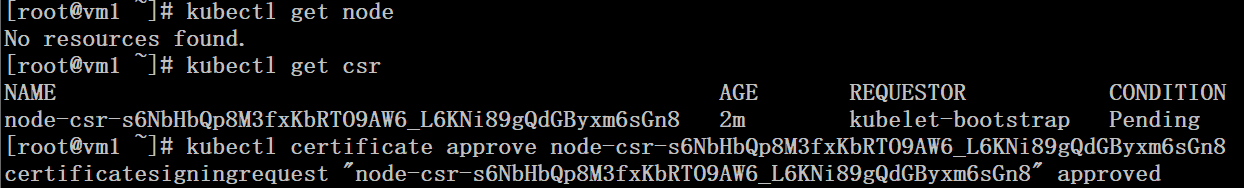
8、在master上對node節點的csr進行授權
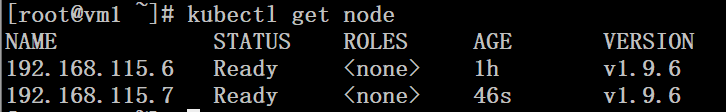
# kubectl get nodes
# kubectl get csr
# kubectl certificate approve node-csr-s6NbHbQp8M3fxKbRTO9AW6_L6KNi89gQdGByxm6sGn8
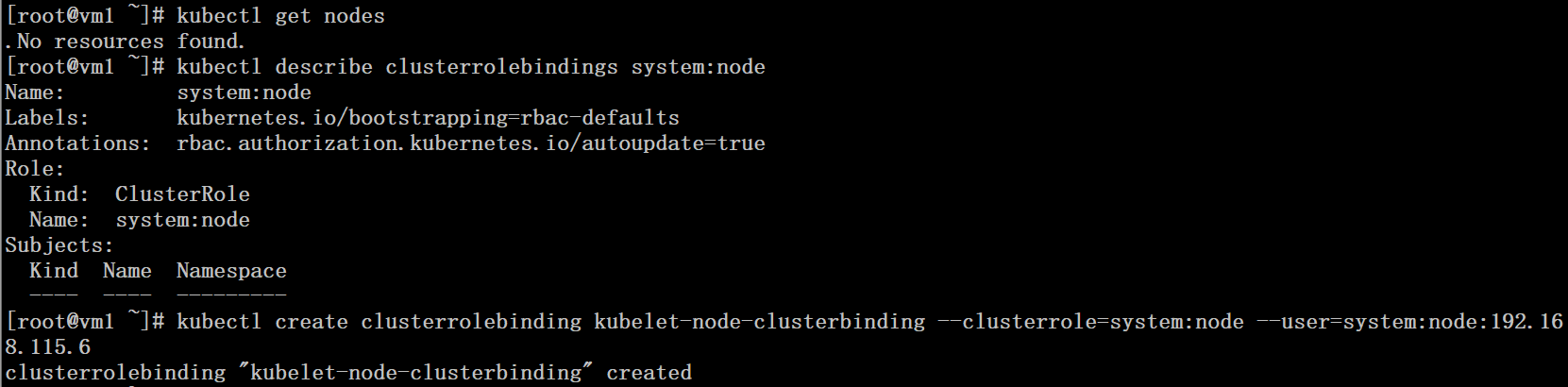
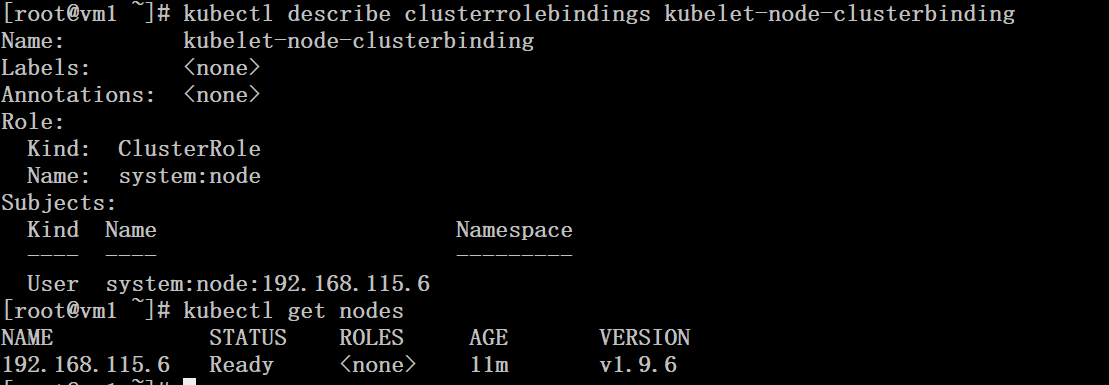
9、在master上進行角色綁定
# kubectl get nodes
# kubectl describe clusterrolebindings system:node
# kubectl create clusterrolebinding kubelet-node-clusterbinding \
--clusterrole=system:node --user=system:node:192.168.115.6# kubectl describe clusterrolebindings kubelet-node-clusterbinding
也可以將在整個集羣範圍內將 system:node ClusterRole 授予組”system:nodes”:
# kubectl create clusterrolebinding kubelet-node-clusterbinding \
> --clusterrole=system:node --group=system:nodes
clusterrolebinding "kubelet-node-clusterbinding" created常見錯誤:
error: failed to run Kubelet: Running with swap on is not supported, please disable swap! or set --fail-swap-on flag to false. /proc/swaps contained:
解決方案:
# swapoff -a四、node節點上設置kube-proxy
1、創建 kube-proxy 證書籤名請求
# cat kube-proxy-csr.json
{
"CN": "system:kube-proxy",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "FuZhou",
"L": "FuZhou",
"O": "k8s",
"OU": "System"
}
]
}
# cfssl gencert -ca=/etc/ssl/etcd/ca.pem \
-ca-key=/etc/ssl/etcd/ca-key.pem \
-config=/etc/ssl/etcd/ca-config.json \
-profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy
# mv kube-proxy*.pem /etc/ssl/kubernetes/
# rsync /etc/ssl/kubernetes/* vm2:/etc/ssl/kubernetes/
# rsync /etc/ssl/kubernetes/* vm3:/etc/ssl/kubernetes/2、在node節點上創建 kube-proxy kubeconfig 文件
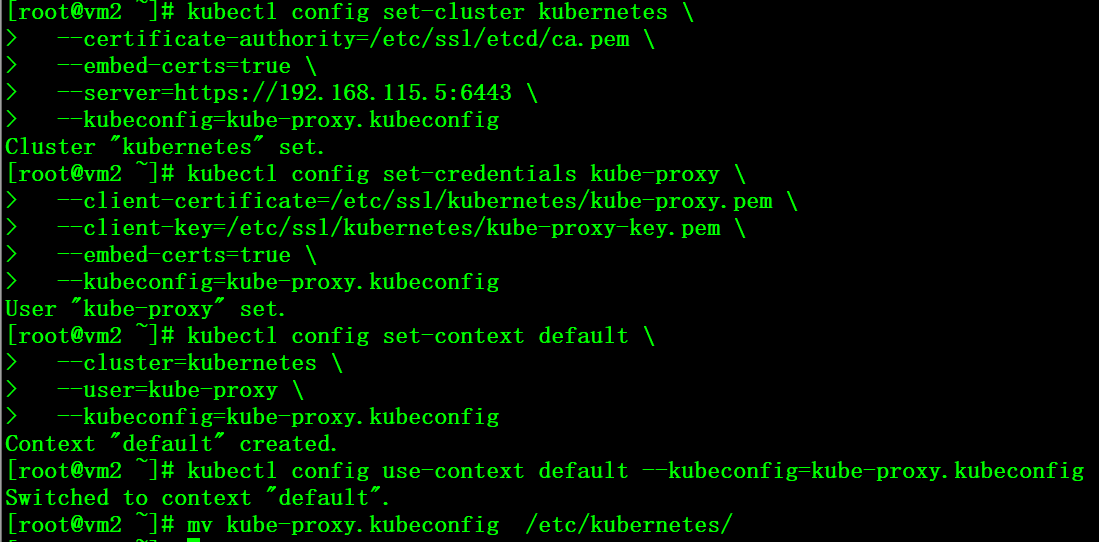
設置集羣參數
# kubectl config set-cluster kubernetes \
--certificate-authority=/etc/ssl/etcd/ca.pem \
--embed-certs=true \
--server=https://192.168.115.5:6443 \
--kubeconfig=kube-proxy.kubeconfig設置客戶端參數
# kubectl config set-credentials kube-proxy \
--client-certificate=/etc/ssl/kubernetes/kube-proxy.pem \
--client-key=/etc/ssl/kubernetes/kube-proxy-key.pem \
--embed-certs=true \
--kubeconfig=kube-proxy.kubeconfig設置上下文參數
# kubectl config set-context default \
--cluster=kubernetes \
--user=kube-proxy \
--kubeconfig=kube-proxy.kubeconfig設置默認上下文
# kubectl config use-context default --kubeconfig=kube-proxy.kubeconfig
# mv kube-proxy.kubeconfig /etc/kubernetes/
3、創建kube-proxy工作目錄
# mkdir -p /var/lib/kube-proxy4、配置kube-proxy啓動腳本
# cat /usr/lib/systemd/system/kube-proxy.service
[Unit]
Description=Kubernetes Kube-Proxy Server
Documentation=https://github.com/GoogleCloudPlatform/kubernetes
After=network.target
[Service]
WorkingDirectory=/var/lib/kube-proxy
ExecStart=/usr/local/sbin/kube-proxy \
--bind-address=192.168.115.6 \
--hostname-override=192.168.115.6\
--cluster-cidr=172.30.0.0/16 \
--kubeconfig=/etc/kubernetes/kube-proxy.kubeconfig \
--logtostderr=true \
--v=2
Restart=on-failure
RestartSec=5
LimitNOFILE=65536
[Install]
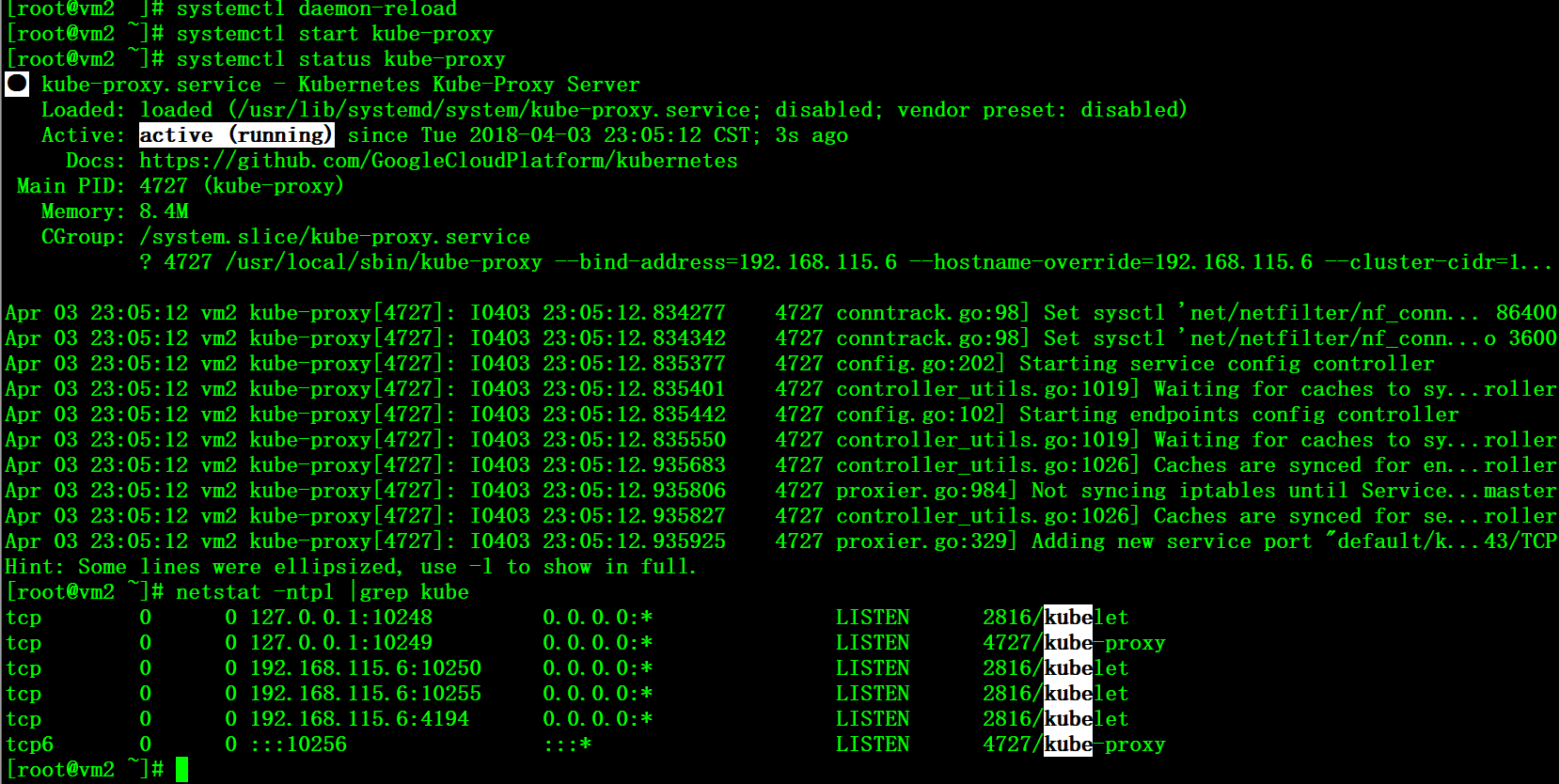
WantedBy=multi-user.target5、啓動測試
# systemctl daemon-reload
# systemctl start kube-proxy
# netstat -ntpl |grep kube
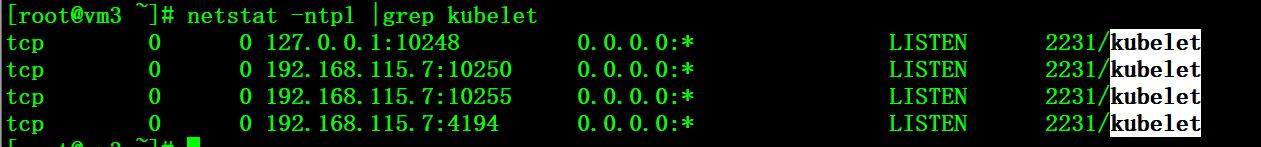
按照同樣的方法部署另一臺node主機vm3
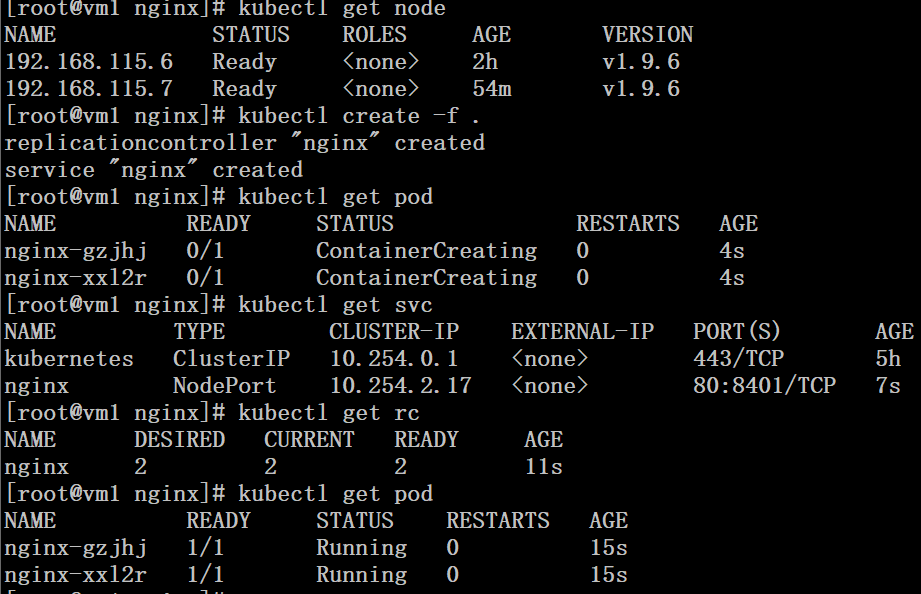
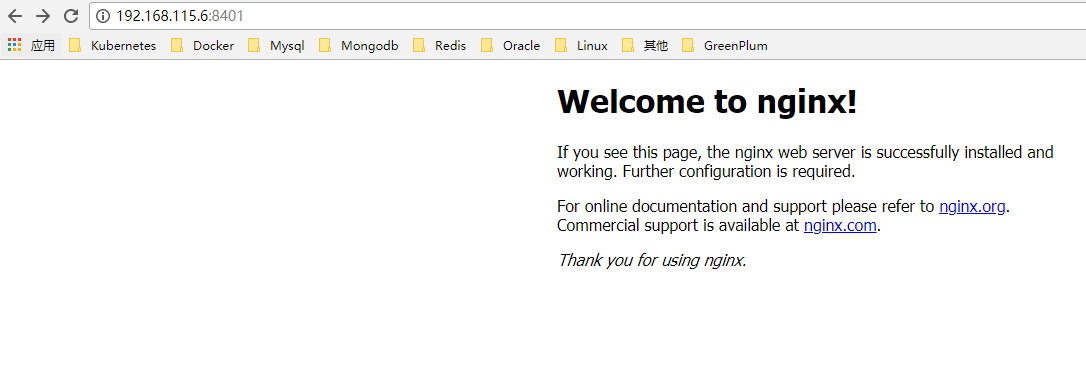
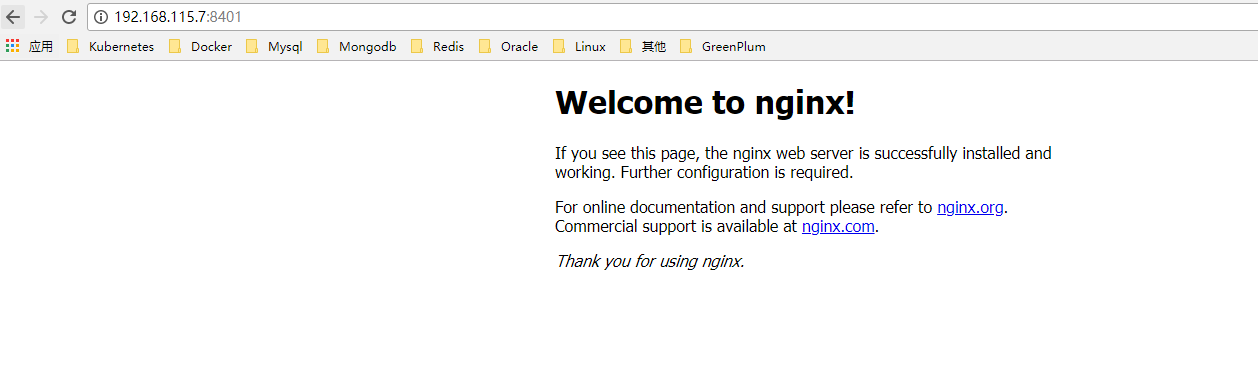
五、創建pod測試
# cat nginx-rc.yaml
apiVersion: v1
kind: ReplicationController
metadata:
name: nginx
labels:
name: nginx
spec:
replicas: 2
selector:
name: nginx
template:
metadata:
labels:
name: nginx
spec:
containers:
- name: nginx-test
image: docker.io/nginx
ports:
- containerPort: 80
# cat nginx-svc.yaml
apiVersion: v1
kind: Service
metadata:
name: nginx
labels:
name: nginx
spec:
type: NodePort
ports:
- port: 80
protocol: TCP
targetPort: 80
name: http
nodePort: 8401
selector:
name: nginx
訪問測試