ASA
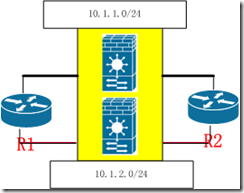
mode multiple ---查看 show mode
firewall transparent ---查看 show firewall
hostname ASA ---牆的命名
interface Ethernet0/0 ---四個接口no shutdown
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
admin-context admin ---定義一個admin的牆,子牆可以起名爲c1和c2,也可以直接用admin
context admin
allocate-interface Ethernet0/0 inside ---如果這裏打inside,那麼在子牆下面看到的不再是接口Ethernet0/0,而是inside
allocate-interface Ethernet0/2 outside
config-url disk0:/admin.cfg ---配置保存目錄
!
context c1
allocate-interface Ethernet0/1 inside
allocate-interface Ethernet0/3 outside
config-url disk0:/c1.cfg
!
切換到子牆
changeto context admin
changeto context c1
切換回到全局
changeto system
__________________________________________________________________________
hostname admin
interface inside
nameif inside --- 定義安全級別
security-level 100 ---inside默認爲100,爲最高,其餘的都爲0
!
interface outside
nameif outside
security-level 0
ip address 10.1.1.100 255.255.255.0 ---每個子牆下面要寫一條和防火牆兩側同一網段的ip 地址 必須
access-list out extended permit icmp any any ---放行icmp,用於測試
access-group out in interface outside ---調用列表
_____________________________________________________________________________
hostname c1
interface inside
nameif inside --- 定義安全級別
security-level 100 ---inside默認爲100,爲最高,其餘的都爲0
!
interface outside
nameif outside
security-level 0
ip address 10.1.2.100 255.255.255.0 ---每個子牆下面要寫一條地址 必須。 經過測試,隨便寫個地址也可以通
access-list out extended permit icmp any any --- 放行icmp,用於測試
access-group out in interface outside ---調用列表
____________________________________________________________________________-
多模下有包分類,即traffic如何知道到那個子牆下,ASA定義了三種包分類:有優先級
- unique interface
- unique mac (在share interface情況下,即第一條不滿足的情況。可以使用mac auto,也可以自定義mac ,常用的是mac auto)
- nat configuration
http://www.cisco.com/en/US/docs/security/asa/asa80/configuration/guide/fwmode.html#wp1201980
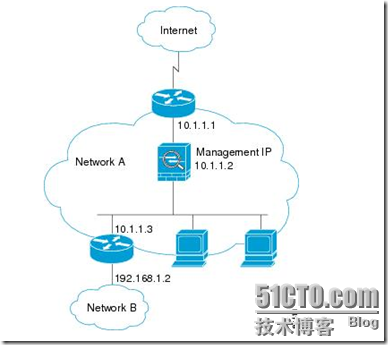
cisco給出的圖片