calico 支持ipip、BGP路由 (屬於三層技術) ,使用虛擬路由代替虛擬交換,每一臺虛擬路由通過BGP協議傳播可達信息(路由)到剩餘數據中心。
參考 :https://docs.projectcalico.org/v3.2/getting-started/kubernetes/installation/flannel
將calico 與 flannel整合後的項目就是canal 。可以利用canal的策略來控制Pods之間的隔離。canal 支持的版本 1.10+ ,要求kubernetes 啓用CNI插件,必須通過傳遞--network-plugin=cni參數將kubelet配置爲使用CNI網絡( kubeadm安裝方式中這是默認設置)。要求支持kube-proxy的模式爲 iptable ,而ipvs模式需要1.9以上。且確保環境中etcd正常工作,確保k8s設置了--cluster-cidr=10.244.0.0/16和--allocate-node-cidrs=true (kubeadm安裝方式這些是默認的,可見/etc/kubernetes/manifests/kube-controller-manager.yaml文件)
部署canal
1) 部署RBAC
[root@docker79 manifests]# mkdir calico
[root@docker79 manifests]# cd calico/
[root@docker79 calico]# wget https://docs.projectcalico.org/v3.2/getting-started/kubernetes/installation/hosted/canal/rbac.yaml
--2018-09-11 17:51:19-- https://docs.projectcalico.org/v3.2/getting-started/kubernetes/installation/hosted/canal/rbac.yaml
正在解析主機 docs.projectcalico.org (docs.projectcalico.org)... 35.189.132.21
正在連接 docs.projectcalico.org (docs.projectcalico.org)|35.189.132.21|:443... 已連接。
已發出 HTTP 請求,正在等待迴應... 200 OK
長度:2469 (2.4K) [application/x-yaml]
正在保存至: “rbac.yaml”
100%[======================================>] 2,469 --.-K/s 用時 0s
2018-09-11 17:51:20 (83.1 MB/s) - 已保存 “rbac.yaml” [2469/2469])
[root@docker79 calico]# kubectl apply -f rbac.yaml
clusterrole.rbac.authorization.k8s.io/calico created
clusterrole.rbac.authorization.k8s.io/flannel configured
clusterrolebinding.rbac.authorization.k8s.io/canal-flannel created
clusterrolebinding.rbac.authorization.k8s.io/canal-calico created
[root@docker79 calico]#2) 部署canal
[root@docker79 calico]# wget https://docs.projectcalico.org/v3.2/getting-started/kubernetes/installation/hosted/canal/canal.yaml
--2018-09-11 17:51:57-- https://docs.projectcalico.org/v3.2/getting-started/kubernetes/installation/hosted/canal/canal.yaml
正在解析主機 docs.projectcalico.org (docs.projectcalico.org)... 35.189.132.21
正在連接 docs.projectcalico.org (docs.projectcalico.org)|35.189.132.21|:443... 已連接。
已發出 HTTP 請求,正在等待迴應... 200 OK
長度:11237 (11K) [application/x-yaml]
正在保存至: “canal.yaml”
100%[======================================>] 11,237 --.-K/s 用時 0.001s
2018-09-11 17:51:58 (18.2 MB/s) - 已保存 “canal.yaml” [11237/11237])
[root@docker79 calico]# kubectl apply -f canal.yaml
configmap/canal-config created
daemonset.extensions/canal created
serviceaccount/canal created
customresourcedefinition.apiextensions.k8s.io/felixconfigurations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/bgpconfigurations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/ippools.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/hostendpoints.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/clusterinformations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/globalnetworkpolicies.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/globalnetworksets.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/networkpolicies.crd.projectcalico.org created
[root@docker79 calico]#
[root@docker79 calico]# kubectl get pods -n kube-system
NAME READY STATUS RESTARTS AGE
canal-cbspc 3/3 Running 0 1m
canal-cq7kq 0/3 ContainerCreating 0 1m
canal-kzd46 3/3 Running 0 1m
coredns-78fcdf6894-pn4s2 1/1 Running 0 14d
coredns-78fcdf6894-sq7vg 1/1 Running 0 14d
etcd-docker79 1/1 Running 0 14d
kube-apiserver-docker79 1/1 Running 0 14d
kube-controller-manager-docker79 1/1 Running 0 14d
kube-flannel-ds-amd64-29j4r 1/1 Running 0 36m
kube-flannel-ds-amd64-f2fsk 1/1 Running 0 36m
kube-flannel-ds-amd64-g9wlf 1/1 Running 0 36m
kube-proxy-c78x5 1/1 Running 2 14d
kube-proxy-hhxrh 1/1 Running 0 14d
kube-proxy-k8hgk 1/1 Running 0 14d
kube-scheduler-docker79 1/1 Running 0 14d
kubernetes-dashboard-767dc7d4d-hpxbb 1/1 Running 0 7h
[root@docker79 calico]#canal 策略
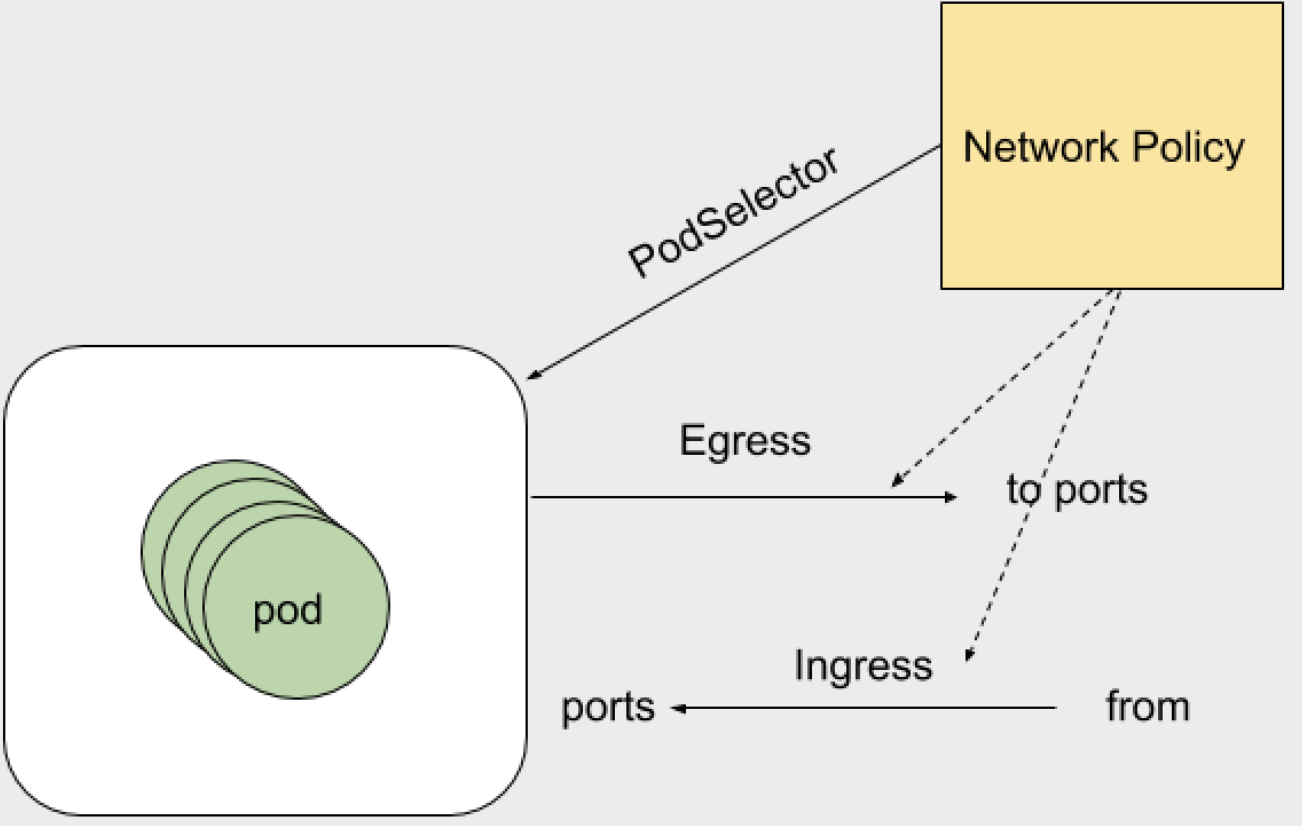
- Egress 表示出站流量,pod作爲客戶端訪問外部服務,pod地址作爲源地址。策略可以定義目標地址或者目的端口
- Ingress 表示入站流量,pod地址和服務作爲服務端,提供外部訪問。pod地址作爲目標地址。策略可以定義源地址和自己端口
- podSelector 規則生效在那個pod上,可以配置單個pod或者一組pod,可以定義單方向;空 podSelector則選擇本命名空間中所有Pod。
使用 kubectl explain networkpolicy.spec 命令可以看到 egress、ingress、podSelector、policyTypes等選項,詳細如下: - egress 出站流量規則 可以根據ports和to去定義規則。ports下可以指定目標端口和協議。to(目標地址):目標地址分爲ip地址段、pod、namespace
- ingress 入站流量規則 可以根據ports和from。ports下可以指定目標端口和協議。from(來自那個地址可以進來):地址分爲ip地址段、pod、namespace
- podSelector 定義NetworkPolicy的限制範圍。直白的說就是規則應用到那個pod上。podSelector: {},留空就是定義對當前namespace下的所有pod生效。沒有定義白名單的話 默認就是Deny ALL (拒絕所有)
- policyTypes 指定哪個規則生效,不指定就是默認規則。
網絡策略控制實例
1) 創建兩個namespace ,分別是dev、prod,如下所示:
[root@docker79 calico]# kubectl create namespace dev
namespace/dev created
[root@docker79 calico]# kubectl create namespace prod
namespace/prod created2) 定義ingress-def 的策略,並應用到dev namespace,如下所示:
[root@docker79 calico]# vim ingress-def.yaml
[root@docker79 calico]# cat ingress-def.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: deny-all-ingress
spec:
podSelector: {}
policyTypes:
- Ingress
[root@docker79 calico]#
[root@docker79 calico]# kubectl apply -f ingress-def.yaml -n dev
networkpolicy.networking.k8s.io/deny-all-ingress created
[root@docker79 calico]#
[root@docker79 calico]# kubectl get netpol -n dev
NAME POD-SELECTOR AGE
deny-all-ingress <none> 3m
[root@docker79 calico]#3) 在 dev 的 namespace中運行pod,並測試訪問,如下所示:
[root@docker79 calico]# vim pod-1.yaml
[root@docker79 calico]# cat pod-1.yaml
apiVersion: v1
kind: Pod
metadata:
name: pod1
spec:
containers:
- name: myapp
image: ikubernetes/myapp:v1
[root@docker79 calico]#
[root@docker79 calico]# kubectl apply -f pod-1.yaml -n dev
pod/pod1 created
[root@docker79 calico]# kubectl get pods -n dev -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE
pod1 1/1 Running 0 4s 10.244.2.3 docker78 <none>
[root@docker79 calico]#
[root@docker79 calico]# curl 10.244.2.3 <無法訪問>
^C 由於 ingress-def.yaml文件中policyTypes只定義了Ingress ,且Ingress rules沒定義,所以默認拒絕所有(入棧)連接。
4) 在prod名稱空間中運行pod ,並測試訪問,如下所示:
[root@docker79 calico]# kubectl apply -f pod-1.yaml -n prod
pod/pod1 created
[root@docker79 calico]# kubectl get pods -n prod -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE
pod1 1/1 Running 0 21s 10.244.2.4 docker78 <none>
[root@docker79 calico]# curl 10.244.2.4
Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a>
[root@docker79 calico]#由於 prod空間並沒有應用ingress策略,所以運行pod後 可以正常訪問 。
5) 修改dev 名稱空間中的 ingress 策略,並測試訪問,如下所示:
[root@docker79 calico]# vim ingress-def.yaml
[root@docker79 calico]# cat ingress-def.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: deny-all-ingress
spec:
podSelector: {}
ingress:
- {}
policyTypes:
- Ingress
[root@docker79 calico]# kubectl apply -f ingress-def.yaml -n dev
networkpolicy.networking.k8s.io/deny-all-ingress configured
[root@docker79 calico]# curl 10.244.2.3
Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a>
[root@docker79 calico]#由於 ingress-def.yaml文件中policyTypes定義了Ingress,而ingress 字段又定義了允許範圍爲空(表示允許所有訪問)的rule,所以最終可以訪問dev namespace 中的pod。
6)恢復ingress策略中的deny操作,並在dev名稱空間中添加新的ingress 策略,並指定具體的rule,測試如下操作:
[root@docker79 calico]# cat allow-netpol-demo.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-myapp-ingress
spec:
podSelector:
matchLabels:
app: myapp
ingress:
- from:
- ipBlock:
cidr: 10.244.0.0/16
except:
- 10.244.1.2/32
ports:
- protocol: TCP
port: 80
- protocol: TCP
port: 443
[root@docker79 calico]# kubectl apply -f allow-netpol-demo.yaml -n dev
networkpolicy.networking.k8s.io/allow-myapp-ingress created
[root@docker79 calico]# curl 10.244.2.3
Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a>
[root@docker79 calico]#7) 在Prod名稱空間添加egress 策略,如下所示:
[root@docker79 calico]# vim egress-def.yaml
[root@docker79 calico]# cat egress-def.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: deny-all-egress
spec:
podSelector: {}
policyTypes:
- Egress
[root@docker79 calico]# kubectl apply -f egress-def.yaml -n prod
networkpolicy.networking.k8s.io/deny-all-egress created
[root@docker79 calico]# kubectl get pods -n prod
NAME READY STATUS RESTARTS AGE
pod1 1/1 Running 0 23m
[root@docker79 calico]# kubectl exec pod1 -it -n prod -- /bin/sh
/ # ping 10.244.0.2
PING 10.244.0.10 (10.244.0.2): 56 data bytes
^C
--- 10.244.0.2 ping statistics ---
4 packets transmitted, 0 packets received, 100% packet loss
/ # command terminated with exit code 1
[root@docker79 calico]# 由於沒有定義egress 的rules ,所以默認deny all,導致prod名稱空間中的pod不能出棧。
8) 修改prod 名稱空間中的egress策略,並添加 egress rules ,如下所示:
[root@docker79 calico]# vim egress-def.yaml
[root@docker79 calico]# cat egress-def.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: deny-all-egress
spec:
podSelector: {}
egress:
- {}
policyTypes:
- Egress
[root@docker79 calico]# kubectl apply -f egress-def.yaml -n prod
networkpolicy.networking.k8s.io/deny-all-egress configured
[root@docker79 calico]# kubectl exec pod1 -it -n prod -- /bin/sh
/ # ping 10.244.0.2
PING 10.244.0.2 (10.244.0.2): 56 data bytes
64 bytes from 10.244.0.2: seq=0 ttl=62 time=0.649 ms
64 bytes from 10.244.0.2: seq=1 ttl=62 time=0.507 ms
^C
--- 10.244.0.2 ping statistics ---
2 packets transmitted, 2 packets received, 0% packet loss
round-trip min/avg/max = 0.507/0.578/0.649 ms
/ # [root@docker79 calico]#由於egress rule 定義爲空,所以允許所有出棧操作。